Changelog
This page displays a full list of all the changes during our release cycle from v2024.3-eclipse onward. Operators can find here the newest updates together with links to relevant documentation. The list is sorted so that the newest changes appear first.
Note: Any information published on this page was up to date at the time of writing. We do not maintain changelog retrospectively.
Our documentation often refer to syntax annotated in <> brackets. We use this expression for variables that are unique to each user (like path, local moniker, versions etcetra).
Any syntax in <> brackets needs to be substituted with your correct name or version, without the <> brackets. If you are unsure, please check our table of essential parameters and variables (opens in a new tab).
v2025.7-tex
- Release Binaries (opens in a new tab)
nym-nodeversion1.9.0
nym-node
Binary Name: nym-node
Build Timestamp: 2025-04-15T14:36:52.729991996Z
Build Version: 1.9.0
Commit SHA: 08b6be93c49e8c225e74ffabb5529493bd4b13b6
Commit Date: 2025-04-15T15:29:46.000000000+02:00
Commit Branch: HEAD
rustc Version: 1.86.0
rustc Channel: stable
cargo Profile: releaseOperators Updates & Tools
-
Nym release binaries (opens in a new tab) no longer work on distributions Debian bullseye/sid (11) / Ubuntu 20.04 LTS and older! Please upgrade your sever to Debian bookworm (Debian 12) / Ubuntu 22.04 (and newer)! Alternatively compile the binaries from source.
-
The Nym Squad League Winter Season has concluded. Changes are coming to NSL, including the new NSL council, monthly payments for contributions, revamped reports, and more. Details available in the Winter Season report (opens in a new tab).
-
New scripts to inititialise and configure multiple VMs: KVM setup for virtualising nodes proved to be a good approach for admins orchestrating multiple nodes on a dedicated or bare metal machines. Now there is an option of running bash scripts speeding up the process of VM initialisation and configuration, while leaving some flexibility via interactive prompts.
Features
-
Move all workflows on ubuntu-20 to ubuntu-22 (opens in a new tab): Ubuntu 20.04 runners are scheduled to be removed from set of github hosted runners. Now is as good a time as any to finally take the plunge to switch away from ubuntu-20.04 to the shiny oh so modern ubuntu-22.04 runners
-
Bump
ellipticfrom6.5.5to6.6.1(opens in a new tab): Bumpselliptic(opens in a new tab) -
Bump
blake3from1.6.1to1.7.0(opens in a new tab): Bumpsblake3(opens in a new tab) -
Mix throughput tester (opens in a new tab): A utility to measure mixing throughput of a node. Especially since there are some design choices with non-obvious performance penalties. For example 1 bloomfilter per connection vs 1 global bloomfilter with additional locking for replay protection.
-
Update log crate (opens in a new tab): Update
log crateto latest, fixformat_in_format_args, fixto_string_in_format_args -
Bump the patch-updates group across 1 directory with 7 updates (opens in a new tab):
| Package | From | To |
|---|---|---|
clap (opens in a new tab) | 4.5.32 | 4.5.34 |
clap_complete (opens in a new tab) | 4.5.46 | 4.5.47 |
once_cell (opens in a new tab) | 1.21.1 | 1.21.3 |
reqwest (opens in a new tab) | 0.12.4 | 0.12.15 |
tempfile (opens in a new tab) | 3.19.0 | 3.19.1 |
time (opens in a new tab) | 0.3.39 | 0.3.41 |
uniffi (opens in a new tab) | 0.29.0 | 0.29.1 |
-
Improve explorer caching (opens in a new tab): Fix:
tanstackcaching- graphs data bug
- "auto" gas fee for redeem rewards
-
Bash scripts to init and configure VMs conveniently and update docs (opens in a new tab): KVM setup for virtualising nodes proved to be a good approach for admins orchestrating multiple nodes on a dedicated/bare machines. This PR adds an option of running bash scripts speeding up the process of VM initialisation and configuration, while leaving some flexibility to the users via interactive prompts.
- Script to initialise new VM on host machine and prompting user for needed vars
- Script to config the VM from within and prompting user for needed vars
- Documentation of the above
- Lift headers so the main chapters come out in the side menu for easier navigation
-
Expand
/v3/nym-nodeswith geodata (opens in a new tab): Includes node description and geodata.
Bugfix
-
Minor fixes involving key cloning and hashing (opens in a new tab): Adds fixes for several minor key related issues:
- Copying a private keys to perform a DH
- Perform DH against the reference to the static key to prevent memory copy of secret key material
- Hashing an
x25519public key without first converting to a canonical representation - Use derived
Hashimplementation which internally converts to a canonical representation (opens in a new tab) before hashing
v2025.6-chuckles
- Release Binaries (opens in a new tab)
nym-nodeversion1.8.0
nym-node
Binary Name: nym-node
Build Timestamp: 2025-04-01T09:55:02.982234741Z
Build Version: 1.8.0
Commit SHA: a429d6528e99b878a310b71bdbe6d31923c52d84
Commit Date: 2025-04-01T11:41:15.000000000+02:00
Commit Branch: HEAD
rustc Version: 1.85.1
rustc Channel: stable
cargo Profile: releaseOperators Updates & Tools
-
Nym Wallet v1.2.16 (opens in a new tab): Operators can change their parameters in the GUI interface again. Remember that while changing node settings will take effect in the next epoch (max 60 min), Operator cost and Profit margin will be updated with the change of interval (720 epochs). You can track the state of epochs and intervals here (opens in a new tab). Currently we are less than 24h from the end of interval, if you were to change OC or PM, do it now!
-
Nym Explorer v2.1.0 (opens in a new tab) is out as a beta release
-
Since last release Wireguard exit policy is out!. Make sure to apply it on the servers hosting
nym-nodeinexit-gatewaymode.
Community Tools
Nym operators are coming with diverse backgrounds. While for some running a nym-node is an introduction to sys-administration, others are well seasoned builders and hackers. It's amazing to see the effort people put in order to lift each other by day-to-day mutual problem solving support in Matrix channel (opens in a new tab). More and more people take it further and build tools to improve network monitoring and node administration.
While we are planning to make a page aggregating these tools together, here are some tools released lately by the technical community:
-
SpectreDAO token dashboard (opens in a new tab): Including stats, distribution, alongside all fundamental stats
-
SpectreDAO privacy check (opens in a new tab): Testing users browser, IP info, WebRTC leaks, fingerprinting, extensions and most importantly whether you access via NymVPN (opens in a new tab)
-
Service status dashboards: Uptime dashboards showing status of Nym Nodes, either squads using self-hosted Uptime Kuma (opens in a new tab) or a custom dashboard, like the one from Oceanus (opens in a new tab)
-
Nym Node Widget (opens in a new tab): A MacOS widget following status of your nodes by koutakou (opens in a new tab)
-
Nymesis (opens in a new tab): Beta version of an explorer tracking node rewards in a simple graph
Features
-
Bump
http-proxy-middlewarefrom2.0.6to2.0.7(opens in a new tab): Bumpshttp-proxy-middleware(opens in a new tab) -
Bump
nextfrom13.5.7to14.2.15in/documentation/docs(opens in a new tab): Bumpsnext(opens in a new tab) -
Bump
nextfrom14.1.4to14.2.21in/explorer-nextjs(opens in a new tab): Bumpsnext(opens in a new tab) -
Bump
nanoidfrom3.3.7to3.3.8in/documentation/docs(opens in a new tab): Bumpsnanoid(opens in a new tab) -
Bump
store2from2.14.3to2.14.4(opens in a new tab): Bumpsstore2(opens in a new tab) -
Bump
@octokit/plugin-paginate-restand@actions/githubin/.github/actions/nym-hash-releases/src(opens in a new tab): Bumps@octokit/plugin-paginate-rest(opens in a new tab) -
Clean stale partially received buffers (opens in a new tab): Clean up old
ReconstructionBuffers that have not received fragments in a long time. The motivation is that we want to allow the client to cap the number of re-transmissions done, meaning we can't assume that these will eventually arrive -
Bump
bracesfrom3.0.2to3.0.3in/sdk/typescript/packages/mix-fetch-node(opens in a new tab): Bumpsbraces(opens in a new tab) -
Bump
golang.org/x/netfrom0.23.0to0.36.0in/wasm/mix-fetch/go-mix-conn(opens in a new tab): Bumps golang.org/x/net (opens in a new tab) -
Bump
wsfrom8.13.0to8.18.1in/wasm/client/internal-dev(opens in a new tab): Bumpsws(opens in a new tab) -
Bump webpack from
5.77.0to5.98.0in/wasm/client/internal-dev(opens in a new tab): Bumpswebpack(opens in a new tab) -
Feature/paginated ticketbooks challenge (opens in a new tab): This PR makes changes to how ticketbook rewarding works and in particular the challenge portion of the exchange. Rather than requesting merkle proof alongside all binary data of the associated ticketbooks in a single
/issued-ticketbooks-challengequery (that could have potentially lead to ddos of nym-apis as it made them load all of the data into the memory at once) the query got split into/issued-ticketbooks-challenge-commitmentfor obtaining the merkle proof and/issued-ticketbooks-datafor obtaining the binary data. Note that the latter query might have to be called multiple times with different arguments due to the enforced limit on the maximum number of values returned at once.
- added:
/issued-ticketbooks-count/issued-ticketbooks-for-count/:expiration_date/issued-ticketbooks-on-count/:issuance_date/issued-ticketbooks-challenge-commitment/issued-ticketbooks-data
- removed:
/issued-ticketbooks-challenge
Testing Steps Performed: New issue ticketbook related endpoints work - tickets are issued and consumed as before. Redeeming tickets is happening as normal on the gateway side.
Notes (if any): Chuckles will not require the rewarder binary to be updated; as there will be additional changes to rewarding, this will be extensively tested in the future.
-
Bump
@babel/runtimefrom7.16.3to7.26.10in/testnet-faucet(opens in a new tab): Bumps@babel/runtime(opens in a new tab) -
Bump the
patch-updatesgroup with 8 updates (opens in a new tab):
| Package | From | To |
|---|---|---|
async-trait (opens in a new tab) | 0.1.87 | 0.1.88 |
clap (opens in a new tab) | 4.5.31 | 4.5.32 |
env_logger (opens in a new tab) | 0.11.6 | 0.11.7 |
http-body-util (opens in a new tab) | 0.1.2 | 0.1.3 |
quote (opens in a new tab) | 1.0.39 | 1.0.40 |
tokio (opens in a new tab) | 1.44.0 | 1.44.1 |
tokio-util (opens in a new tab) | 0.7.13 | 0.7.14 |
indexed_db_futures (opens in a new tab) | 0.6.0 | 0.6.1 |
-
Bump
humantimefrom2.1.0to2.2.0(opens in a new tab): Bumpshumantime(opens in a new tab) -
Bump
httpfrom1.2.0to1.3.1(opens in a new tab): Bumpshttp(opens in a new tab) -
Bump
uuidfrom1.15.1to1.16.0(opens in a new tab): Bumpsuuid(opens in a new tab) -
Bump
once_cellfrom1.20.3to1.21.1(opens in a new tab): Bumpsonce_cell(opens in a new tab) -
Bump
zeroizefrom1.6.0to1.8.1(opens in a new tab): Bumpszeroize(opens in a new tab) -
Bump
tempfilefrom3.18.0to3.19.0(opens in a new tab): Bumpstempfile(opens in a new tab) -
Rework IPR codec to extract out timer and implement AsyncWrite (opens in a new tab): The goal is to be able to handle back pressure in the vpn client. For that we need to extract out the timer from the codec since we want to move control over that to the mixnet processor. Once the timer is removed we can reformulate the mixnet sender as a
Sinkwrapped in aFramedWrite- Extract out timer from IPR codec
- Implement AsyncWrite on mixnet client sender
- Add functions to wait for lanes to clear on
LaneQueueLenghts
-
Remove
explorer-apifrom the main workspace (opens in a new tab) -
Bump
dtolnay/rust-toolchainfrom1.90.0to1.100.0(opens in a new tab): Bumpsdtolnay/rust-toolchain(opens in a new tab) -
Bump
zipfrom2.2.2to2.4.1(opens in a new tab): Bumpszip(opens in a new tab) -
Add
max_retransmissionsflag on each message (opens in a new tab): Add an optionalmax_retransmissionsfield onInputMessage, to be able to selectively disable or turn down the number ofretransmissionsdone for specific packets -
Upgrade
sha2to workspace version for validator-client (opens in a new tab) -
Add
RUSTUP_PERMIT_COPY_RENAMEin two workflows that we forgot about (opens in a new tab) -
Remove
UNIQUEconstraint on node pubkey (opens in a new tab): This accounts for the case when a node rebonds with the same key remove nodes that weren't updated in a week -
Add concurrency limit to CI (opens in a new tab): For
ci-buildworkflow only -
Update wallet to include Interval Operator Cost and Profit Margin (opens in a new tab): Created a new modal for Interval Operator Cost and Profit Margin changes
- Uses existing update node operating cost functionality for old mixnodes (If it works it works)
- Prompts a warning that a user "Can send the request as many times as they want but it will only update the last message when the interval changes"
-
Wallet-revamp to be in line with new nym-theming (opens in a new tab): Updating colour palette to match the nym.com (opens in a new tab) sites:
- Used the same font too
- Updated icons
-
Add
fdcallback for initial authentication (opens in a new tab): One thing that was missed was the registrationwsconnection that happens before the actual connection, if it's the first time connecting to a gateway. This PR extends connectionfdcallback to that initial connection, so that it can also be allowed by firewalls. -
Revert using
AsyncWritesink in IPR (opens in a new tab): Revert the use of theAsyncWritesink in the IPR until it's fully ready. -
Remove Google public DNS (opens in a new tab): We had a lot of complaints about Google, so we're removing this in VPN client, Nym should follow to avoid issues with firewall.
Bugfix
- Corrected typos (opens in a new tab) in
CHANGELOG.md
v2025.5-chokito
- Release Binaries (opens in a new tab)
nym-nodeversion1.7.0
nym-node
Binary Name: nym-node
Build Timestamp: 2025-03-18T12:17:10.782554174Z
Build Version: 1.7.0
Commit SHA: 82e82943aa14e530ab4eb3aaab28ce86d47e5298
Commit Date: 2025-03-18T10:39:55.000000000+01:00
Commit Branch: HEAD
rustc Version: 1.85.0
rustc Channel: stable
cargo Profile: releaseRelease Summary
-
WebSocket Connection Counter Fix (this is the fix for which we have a pre-release branch (opens in a new tab) out already which will be replaced by this release): Prevents incorrect session tracking for WebSockets
-
Security Fixes in Dependencies: Address known security vulnerabilities, making updating highly recommended
-
Authorisation & Timestamp Changes: Modifies how timestamps are validated in Auth v2 - this is going to be what the clients use. For example: the clients will start to use v2 variants of everything (prepping the network for the breaking change to come on April 1st which will force clients to only use v2).
-
Wireguard exit policy scripts (opens in a new tab)
Operators Updates & Tools
-
Wireguard exit policy is out! Operators can use a new guide with our scripts to setup wireguard exit policy using IP tables rules.
-
Setup commands for
nym-nodesimplified:config.tomldefaults to correct binding addresses and ports, no need to specify unless operators want to change those values. -
Virtualising dedicated server with KVM now includes IPv6 setup: Thanks to LunarDAO (opens in a new tab) squad we caught a missing IPv6 configuration in KVM installation guide. Operators can now run a bare metal or dedicated server and virtualise it into VMs each with a fully functional node, having all specs fully under control.
-
NTP time synchronization guide: Some servers had an issue with incorrect time. Please use this guide to update time on your server to synchronize your node operation with the rest of the network.
-
New community managed token page by SpectreDAO (opens in a new tab): Based on community request, one of the squad administrating several Nym Nodes created a live token dashboard explorer.nym.spectredao.net/token (opens in a new tab).
Features
-
Display error messages if IPv4 or IPv6 address not found on nymtun0 (opens in a new tab): This is with regards to issue #5461 (opens in a new tab)
-
Connection
fdcallback before actual connection (opens in a new tab) -
Treat Gateways as Nym Nodes (opens in a new tab): entry/exit nodes are also scraped for description & packets mixed data. Generate a random moniker for nodes that don't have one set.
-
Bump the patch-updates group with 2 updates (opens in a new tab): log (opens in a new tab) and tar (opens in a new tab).
-
Bump itertools from
0.13.0to0.14.0(opens in a new tab): Bumps itertools (opens in a new tab). -
Bump flate2 from
1.0.35to1.1.0(opens in a new tab): Bumps flate2 (opens in a new tab). -
Make sure any terminated task kills the watcher and write run info to db (opens in a new tab)
-
Make "Memo" visible per default on send NYM (opens in a new tab)
-
Disallow routing mix packets to nodes not present in the topology (opens in a new tab)
-
Set
RUSTUP_PERMIT_COPY_RENAME(opens in a new tab): Try to fix rustup issues on our self-hosted runners by settingRUSTUP_PERMIT_COPY_RENAME -
v2 authentication request (opens in a new tab): This PR creates new v2 variant of client-gateway authentication message that increases protection against possible connection hijacking.
-
Bump
rs_merklefrom1.4.2to1.5.0(opens in a new tab): Bumps rs_merkle (opens in a new tab) -
Bump
uuidfrom1.13.2to1.15.1(opens in a new tab): Bumpsuuid(opens in a new tab) -
Bump the
patch-updatesgroup across 1 directory with 14 updates (opens in a new tab):
| Package | From | To |
|---|---|---|
anyhow (opens in a new tab) | 1.0.96 | 1.0.97 |
async-trait (opens in a new tab) | 0.1.86 | 0.1.87 |
blake3 (opens in a new tab) | 1.6.0 | 1.6.1 |
chrono (opens in a new tab) | 0.4.39 | 0.4.40 |
clap (opens in a new tab) | 4.5.30 | 4.5.31 |
clap_complete (opens in a new tab) | 4.5.45 | 4.5.46 |
console (opens in a new tab) | 0.15.10 | 0.15.11 |
getset (opens in a new tab) | 0.1.4 | 0.1.5 |
pin-project (opens in a new tab) | 1.1.9 | 1.1.10 |
quote (opens in a new tab) | 1.0.38 | 1.0.39 |
schemars (opens in a new tab) | 0.8.21 | 0.8.22 |
serde_bytes (opens in a new tab) | 0.11.15 | 0.11.16 |
serde_json (opens in a new tab) | 1.0.139 | 1.0.140 |
thiserror (opens in a new tab) | 2.0.11 | 2.0.12 |
-
Add /v3/nym-nodes (opens in a new tab): Returns extended node info from local DB
- Endpoint caching
- Add
bond_info&self_describedto DBnym_nodes - Update mixnode & gateway bond status on data refresh
- Add
activecolumn to DBnym_nodes - Use only active & bonded nodes in scraping/testrun tasks
-
Rust SDK SURB example: change hardcoded file to tempdir (opens in a new tab): Change hardcoded filepath for client to tempdir
-
Server Side internal DoT/DoH opt out (opens in a new tab): Allow server side (nodes and nym-api) to use nym-http-api-client without DoH/DoT resolver.
-
Bump ring from
0.17.3to0.17.13in /nym-wallet (opens in a new tab): Bumps ring (opens in a new tab) -
Bump the patch-updates group with 8 updates (opens in a new tab):
| Package | From | To |
|---|---|---|
bytes (opens in a new tab) | 1.10.0 | 1.10.1 |
semver (opens in a new tab) | 1.0.25 | 1.0.26 |
serde (opens in a new tab) | 1.0.218 | 1.0.219 |
serde_bytes (opens in a new tab) | 0.11.16 | 0.11.17 |
serde_derive (opens in a new tab) | 1.0.218 | 1.0.219 |
serde_repr (opens in a new tab) | 0.1.19 | 0.1.20 |
time (opens in a new tab) | 0.3.37 | 0.3.39 |
ff (opens in a new tab) | 0.13.0 | 0.13.1 |
-
Bump
tokiofrom1.43.0to1.44.0(opens in a new tab): Bumps tokio (opens in a new tab) -
Bump
tempfilefrom3.17.1to3.18.0(opens in a new tab): Bumps tempfile (opens in a new tab) -
[Bump
webpack-dev-middlewarefrom5.3.3to5.3.4in/wasm/zknym-lib/internal-dev](https://github.com/nymtech/nym/pull/5589 (opens in a new tab)): Bumps webpack-dev-middleware (opens in a new tab) -
Bump
bracesfrom3.0.2to3.0.3in /wasm/zknym-lib/internal-dev (opens in a new tab): Bumps braces (opens in a new tab) -
Bump
cookieandexpressin/wasm/client/internal-dev(opens in a new tab): Bumps cookie (opens in a new tab) -
Bump
wsfrom8.13.0to8.18.1in/wasm/mix-fetch/internal-dev(opens in a new tab): Bumps ws (opens in a new tab) -
Bump
serve-staticandexpressin/wasm/mix-fetch/internal-dev(opens in a new tab): Bumps serve-static (opens in a new tab) -
Bump
body-parserand express in/wasm/mix-fetch/internal-dev(opens in a new tab): Bumps body-parser (opens in a new tab) -
Bump
webpackfrom5.77.0to5.98.0in /wasm/mix-fetch/internal-dev` (opens in a new tab): Bumps webpack (opens in a new tab) -
Introduce internal tool for checking signer status (opens in a new tab)
-
Change
authv2 timestamp skew and allow values from the future (opens in a new tab) -
Bump
@babel/helpersfrom7.24.4to7.26.10(opens in a new tab): Bumps @babel/helpers (opens in a new tab) -
Chore/more payment watcher debug endpoints (opens in a new tab)
-
Export lane queue lengths in sdk (opens in a new tab): Export the lane queue length type to be able to implement backpressure outside of the sdk mixnet client
-
Bump
webpack-dev-middlewarefrom5.3.3to5.3.4in/wasm/client/internal-dev(opens in a new tab): Bumps webpack-dev-middleware (opens in a new tab) -
Bump
bracesfrom3.0.2to3.0.3in/sdk/typescript/packages/nodejs-client(opens in a new tab): Bumps braces (opens in a new tab) -
Remove explorer-api from ci-build-binaries (opens in a new tab)
Bugfix
v2025.4-dorina-patched
Patched version of dorina with a few fixes and tweaks to the release. We would like to ask nym-node operators to upgrade to this version as quickly as possible to implement the fixes across the network and improve general quality before NymVPN launch.
- Release Binaries (opens in a new tab)
nym-nodeversion1.6.2
nym-node
Binary Name: nym-node
Build Timestamp: 2025-03-06T20:32:36.922212778Z
Build Version: 1.6.2
Commit SHA: 247ebb7c4339de0a298a7fcb2574122a8306c3b8
Commit Date: 2025-03-06T21:26:16.000000000+01:00
Commit Branch: HEAD
rustc Version: 1.85.0
rustc Channel: stable
cargo Profile: release- Use legacy crypto for constructing SURB headers (#5579 (opens in a new tab))
- Bugfix: make sure to correctly decode response content when putting it into error message (#5571 (opens in a new tab))
- Tweak surb management to be more conservative (#5570 (opens in a new tab))
- Deserialize v5 authenticator requests (#5568 (opens in a new tab))
- Chore: additional logs when attempting to load ecash keys (#5567 (opens in a new tab))
- Add full response body to error message upon decoding failure (#5566 (opens in a new tab))
- Hotfix: ensure we bail on merkle leaves insertion upon missing data (#5565 (opens in a new tab))
- Feature: v2 authentication request (#5537) (#5563 (opens in a new tab))
- Create authenticator v5 request/response types (#5561 (opens in a new tab))
v2025.4-dorina
- Release Binaries (opens in a new tab)
nym-nodeversion1.6.0
Binary Name: nym-node
Build Timestamp: 2025-03-04T09:03:11.322601809Z
Build Version: 1.6.0
Commit SHA: 7060fa6dad58f17543f5086c73b1854ad1ceae60
Commit Date: 2025-03-03T17:24:10.000000000Z
Commit Branch: release/2025.4-dorina
rustc Version: 1.86.0-nightly
rustc Channel: nightly
cargo Profile: releaseOperators Updates & Tools
- New advanced guide to virtualise a dedicated server, providing steps for experienced operators and aspiring sys-admins who seek for higher optimisation and better efficiency of their work orchestrating multiple nodes.
- New Service Grant program is being implemented by operators setting up new ~150 Exit Gateways following the updated specs for
nym-node
Features
-
Feature/chain status api (opens in a new tab): this PR introduces
/v1/network/chain-statusendpoint on nym api to give basic information about the current block as seen by this API (with some caching) and updates/healthendpoint to give stall information. -
Add SURBs soft threshold (opens in a new tab): the IPR should try to keep a buffer of available SURBs to reduce latency.
-
Simplify IPR v8 (opens in a new tab): purge stuff from IPR v8 to simplify; use protocol field in v8.
-
Shared instance for DNS AsyncResolver (opens in a new tab): make the
HickoryDnsResolveruse a shared instance by default to limit fd use. Now the multiplenym_http_api_client::Clients that get built should take advantage of a shared connection pool for DNS lookups. If for some reason a client does need an independent AsyncResolver this can still be done with the addedthread_resolverfunction. -
cherry-pick 17d3ff2d775f61aee381d90a304ed416c08f33fc onto dorina (opens in a new tab)
-
cherry-pick 6e5d0dac1b75413c5f09122b0d953f8ec6ef48df onto dorina (opens in a new tab)
-
feat: add config option for maximum number of client connections (opens in a new tab)
-
IPR request types v8 (opens in a new tab): Bump IPR request/response types to v8
-
Support static routes for HTTP requests (opens in a new tab)
-
adjusted TestSetup::new_complex to ensure bonded node's existence (opens in a new tab)
-
Trigger contracts CI on main workspace Cargo changes (opens in a new tab): since the contracts workspace depends on the common code in the main workspace, and since the contracts are critical to not have regressions in, trigger contracts CI on any changes to the workspace Cargo.toml and lock files.
-
Run cargo autoinherit (opens in a new tab): run
cargo autoinheritto move a bunch of dependencies to the workspace level.Cargo.lockremains untouched. -
Disable debug in wasm and wallet workflows too (opens in a new tab)
-
Fix clippy::precedence (opens in a new tab): fix clippy warnings for the Rust beta toolchain.
-
Provide Interval context with node descriptor endpoints (opens in a new tab): add current interval context information to existing enpoints using
build_skimmed_nodes_responseunder the hood. This allows clients checking for a refresh to send theepoch_uidas a query parameter when fetching updates so the server can tell it that there have been no changes, instead of sending duplicate data over and over. The changes in this PR should be backwards compatible and never interfere with existing clients. The additions to theNodeParamsare optional, so there is no error if a client does not send them. Old clients will not sendepoch_uidby accident so they cannot accidentally clear their set of known nodes. In the response the status field is optional so if it is missing (e.g. if a new client talks to an old server) the connection still works. For old clients speaking to new servers, the json parsing will simply ignore extra information not included in the objects json spec.
Made a request to the /api/v1/unstable/nym-nodes/semi-skimmed endpoint:
- without entering an epoch_id
- with entering the current epoch_id
- with entering an old epoch_id
- with entering a future epoch_id All results returned the same data, as expected
-
Add helper to extract a list of sqlite files with journal files wal/shm (opens in a new tab)
-
Add a middleware layer to the nym api allowing for data compression (opens in a new tab): after Testing in a minimal example, this does work as expected. Routes still default to plain encoding, however if a client indicates support for a compressed encoding using the
Accept-Encodingheader then the served response will be compressed with the appropriateContent-Encodingheader. (Proof-of-Concept (opens in a new tab))
Sent requests with and without Accept-Encoding: gzip to observe response behaviour Verified if responses included content-encoding: gzip when compression was requested Checked response file output to confirm actual compression occurred
- Condense core API functionalities and enable gzip decompression for reqwest payloads (opens in a new tab): this PR is intended to take out variables from our usage of HTTP requests in the
nym-http-api-client. To do this the PR: (1) adds theApiClientCoretrait with the minimal feature required to send a request, (2) turns all request sending into trait extension automatically implemented for any type that implementsApiClientCore. This has the benefit of consistent expected behavior for all clients usingnym-http-api-client, including features added going forward. FOR EXAMPLE this pr adds a default header"accept-encoding: gzip;q=1.0, *;q=0.5"which indicates that compression is preferred whenever available. Other features to keep in mind here are things like configurable retries, domain fallbacks, etc. Note: theApiclientinterface could be simplified, but that would require refactoring our downstream usages of the API. For now this isn't necessary asApiClientis implemented automatically so it costs nothing to have it this way. It just allows divergent usage in downstream crates.
Measured nym-api response times before and after updating the API client using curl Checked if the client automatically decompressed Gzip responses
- Seedable clients (opens in a new tab): Adds
DerivationMaterialand accompanying methods to builders.DerivationMaterialencapsulates parameters for deterministic key derivation using HKDF (SHA-512). Use thederive_secret()method to generate a 32-byte secret. To prepare for a new derivation, call thenext()method which increments the index. It is the caller's responsibility to track and persist the derivation index if keys need to be rederived.
let master_key = [0u8; 32]; // your secret master key
let salt = "unique-salt-value".to_string();
let material = DerivationMaterial::new(master_key, 0, salt.as_bytes());
// Derive a secret
let secret = material.derive_secret().expect("Failed to derive secret");
// Prepare for the next derivation
let next_material = material.next();- Remove all recv_with_delay and add shutdown condition to loops in client-core (opens in a new tab): inside client-core we want to prepare the ground for moving a behaviour close to what we have in the vpn client. Remove all the recv_with_delay since we want to just stop. Add shutdown condition to all select loops to guard against the shutdown listener being polled inside the select blocks. Remove unwraps when sending on unbounded channels in case the receiver exits before the sender. Move
TaskClientto be a member field so make it easier to wrap log errors in a shutdown check. Update all fork names to use underscore consistently, since the task separator is hyphen
Validated that all binaries including nym-node, nym-client, nym-network-requester, and nym-socks5-client are behaving well without indicating the presence of any unexpected errors or crashes
-
Disable the test for checking the remaining bandwidth in nym-node-status-api (opens in a new tab): this check fails almost every time on CI, possibly due to rate limiting? It's not good to disable the check, but it's blocking CI as it stands now. Given that we have the check above for locating the ip, we at least have a little coverage.
-
Dz nym node stats (opens in a new tab): removed obsolete fields from stats (blacklisted mixnodes, blacklisted gateways, bonded mixnodes, bonded gateways). Introduced nym-node scraping, beside just mixnodes.
/mixnodes/statsnow returns data for nym-nodes as well, which results in much more accurate "packets mixed" stats.
Bugfix
-
bugfix: dont query for ecash apis unless necessary when spending ticketbooks (opens in a new tab)
-
bugfix: bound check when recovering a reply SURB (opens in a new tab)
-
fix: update fx average rate calcs to ignore 0 values (opens in a new tab)
Chore
-
chore: workspace global panic preventing lints (opens in a new tab)
-
build(deps): bump the patch-updates group across 1 directory with 3 updates (opens in a new tab): updates
clapfrom 4.5.28 to 4.5.30, updatesclapfrom 4.5.28 to 4.5.30, updatesprostfrom 0.13.4 to 0.13.5. -
build(deps): bump http from 1.1.0 to 1.2.0 (opens in a new tab)
-
build(deps): bump utoipa-swagger-ui from 8.0.3 to 8.1.0 (opens in a new tab)
-
build(deps): bump colored from 2.1.0 to 2.2.0 (opens in a new tab)
-
build(deps): bump celes from 2.4.0 to 2.5.0 (opens in a new tab)
-
build(deps): bump the patch-updates group with 2 updates (opens in a new tab): updates
clapfrom 4.5.28 to 4.5.29, updatesprostfrom 0.13.4 to 0.13.5. -
build(deps): bump elliptic from 6.5.4 to 6.6.1 in /docker/typescript_client/upload_contract (opens in a new tab): bumps elliptic (opens in a new tab) from 6.5.4 to 6.6.1.
-
build(deps): bump uniffi_build from 0.25.3 to 0.29.0 (opens in a new tab)
-
build(deps): bump hickory-proto from 0.24.2 to 0.24.3 in /nym-wallet (opens in a new tab)
-
build(deps): bump hickory-proto from 0.24.2 to 0.24.3 (opens in a new tab)
-
build(deps): bump the patch-updates group across 1 directory with 10 updates (opens in a new tab): Bumps the patch-updates group with 10 updates in the directory:
| Package | From | To |
|---|---|---|
| async-trait (opens in a new tab) | 0.1.85 | 0.1.86 |
| clap (opens in a new tab) | 4.5.27 | 4.5.28 |
| comfy-table (opens in a new tab) | 7.1.3 | 7.1.4 |
| hickory-resolver (opens in a new tab) | 0.24.2 | 0.24.3 |
| once_cell (opens in a new tab) | 1.20.2 | 1.20.3 |
| pin-project (opens in a new tab) | 1.1.8 | 1.1.9 |
| serde_json_path (opens in a new tab) | 0.7.1 | 0.7.2 |
| toml (opens in a new tab) | 0.8.19 | 0.8.20 |
| cosmrs (opens in a new tab) | 0.21.0 | 0.21.1 |
| tokio-postgres (opens in a new tab) | 0.7.12 | 0.7.13 |
-
build(deps): bump openssl from 0.10.56 to 0.10.70 in /nym-wallet (opens in a new tab)
-
build(deps): bump hyper from 1.4.1 to 1.6.0 (opens in a new tab)
-
build(deps): bump publicsuffix from 2.2.3 to 2.3.0 (opens in a new tab)
v2025.3-ruta
- Release Binaries (opens in a new tab)
nym-nodeversion1.5.0
nym-node
Binary Name: nym-node
Build Timestamp: 2025-02-13T11:49:34.670488195Z
Build Version: 1.5.0
Commit SHA: a3e19b4563843055b305ea9a397eb1ad84b5c378
Commit Date: 2025-02-10T18:14:47.000000000+01:00
Commit Branch: HEAD
rustc Version: 1.84.1
rustc Channel: stable
cargo Profile: releaseOperators Updates & Tools
- Operators who use Debian based distributions must run their
nym-nodeon Debian bookworm (Debian 12)/ Ubuntu 22.04 (and newer). In case of running older operation system make sure to upgrade your server.
Service Grant Program v2 (SGPv2)
As we announced in hu release notes, we are opened a second iteration Service Grant Program to bootstrap node operations in key target geographies for Nym and ensures the network can provide a good quality of service.
Conditions to join of SGPv2
If you are interested to become a part of SGPv2, read the point below. Do not buy new machines and do not migrate nodes just yet!
- Read specs & rules first
- The program will start from March 1st.
- Accepted participants are expected to run their nodes in assigned location and with new specs by February 28th the latest.
- Squads orchestrating multiple nodes will be prioritized in locations with more slots.
- There is no final budget, neither a size per node as we expect that the next round of Service Grants program will be individual grants of varying sizes, depending on how many nodes, location, specs etc.
- Every participant of SGPv1 can submit for SGPv2 as many nodes as they currently have grant for, more slots may be offered later on.
- New submissions can only do one node per operator unless people come in squads (or DAOs) and can orchestrate multiple nodes on larger dedicated servers.
- Actual locations and approximate slots are listed below. If you want to have a node in a location which is not listed but it's near by some of the listed ones, it's not a problem, be honest in the form so we know where you planning to run nodes.
- February is the last month we proceed with grants under SGPv1.
How to Join
- Have a look at the remaining locations, specs and providers. You can contact them directly and make a calculation how much running a node on their service would cost and what size of a grant you expect to receive.
- To apply for a service grant, the first step is to fill in this form (opens in a new tab) per each node.
- Be responsive on Element for follow up communication.
Locations
These locations and slots are approximate and constantly change based on new operators submissions. Please keep in mind that we are going to chose people with respect to empty slots in the given location at the time of their submission. In case of competing submissions in the same location we will take the one with better specs vs price ratio.
| LOCATION | SLOTS |
|---|---|
| India | 3 |
| Austria | 1 |
| Poland | 1 |
| Russia | 2 |
| Canada | 1 |
| South Africa | 2 |
| Sweden | 2 |
| Latvia | 2 |
| Lithuania | 1 |
| Bahrain | 1 |
| Czech Republic | 1 |
| Denmark | 1 |
| Norway | 1 |
| South Korea | 1 |
| Ukraine | 1 |
| Vietnam | 1 |
| Argentina | 1 |
| Belarus | 1 |
| Croatia | 1 |
| Cyprus | 1 |
| Ecuador | 1 |
| Hungary | 1 |
| Malta | 1 |
| New Zealand | 1 |
ISPs
- Have a look into our ISP list page
- Further you can check out Tor community Good Bad ISPs (opens in a new tab) page
- With any findings or feedback, please add it to this csv (opens in a new tab), issue a Pull Request and ping me for review.
- We will add much more providers in the coming days
Features
-
DNS resolver configuration for internal HTTP client lookups (opens in a new tab): The resolver itself is the set combination of the google, cloudflare, and quad9 endpoints supporting DoH, DoT, and for google DoH3 as well. This resolver implements a fallback mechanism where, should the DNS-over-X resolution fail, a followup resolution will be done using the hosts configured default (e.g.
/etc/resolve.confon linux). -
Uncouple storage reference for bandwidth client (opens in a new tab): Because of the
Storagereference in the bandwidth client, the client can't be separated and used in a different place, as it will be linked to theDisconnectedClient. Cloning it ensures we uncouple this unnecessary dependence. -
MixnetClientcan sendClientRequests(opens in a new tab): Adding a channel to theMixnetClient, so that it can signal to theMixTrafficControllerthat can send aClientRequestvia itsGatewayTransciver. Additionaly adds a sleep to thedisconnectcall as the socket would close before the channel message got processed. -
Use secure DNS for websocket connection establishment (opens in a new tab): Adjust the websocket connection establishment (using
tokio_tungstenite) to use a custom DNS resolver that tries DoH and DoT. Instead of relying on thetokio_tungsteniteto open thetokio::net::TcpStream(which it does here (opens in a new tab)) which would kick in the default network resolver we do the resolution and open theTcpStreamourselves before handing off to the websocket libary. -
Reduce log severity for checking topology validity (opens in a new tab)
-
Change Explorer URL to new smooshed nodes (opens in a new tab)
-
Send shutdown instead of panic when reaching max fail (opens in a new tab): Remove a panic and an unwrap inside
client-corethat is hit occasionally in the vpn client. This is a change that can have wide ranging impact since it changes the task handling and it's insideclient-core, which is used in many components and services, so preventing regressions is important. -
Relocate a validator api function (opens in a new tab): Adds a function to the
nym-validator-clientcrate that hits the network details endpoint and returns an object parsed fromjson. This was floating loose in thenym-vpn-clientrepo. -
Bump the patch-updates group across 1 directory with 9 updates (opens in a new tab)
-
Make
wait_for_graceful_shutdownto be pub (opens in a new tab)
Bugfix
- Fix missing path triggers for CI (opens in a new tab): Fix missing path triggers for CI and sort crate list alphabetically to make it easier to maintain.
v2025.2-hu
- Release Binaries (opens in a new tab)
nym-nodeversion1.4.0
nym-node
Binary Name: nym-node
Build Timestamp: 2025-02-04T09:35:42.399220545Z
Build Version: 1.4.0
Commit SHA: 4c2bf3642e8eec0d55c7753e14429d73ac2d0e99
Commit Date: 2025-02-04T10:29:48.000000000+01:00
Commit Branch: HEAD
rustc Version: 1.84.1
rustc Channel: stable
cargo Profile: releaseOperators Updates & Tools
From nym-node v1.3.0 operators can technically choose multiple functionalities for their nym-node binary (flagged as --mode).
However, the clients are yet to be developed to be able to make a proper selection for multi-mode nodes!
WE ASK OPERATORS TO ASSIGN ONLY ONE FUNCTIONALITY TO --mode OPTION PER NODE. PLEASE SELECT ONE MODE ARGUMENT OUT OF: mixnode or entry-gateway or exit-gateway!
-
Updated maintenance guides to backup, restore and move a node, containing a new and important commands to backup and restore
clients.sqlitedatabase. -
New explanation of
nym-nodefunctionalities describing how Gateways get selected in Mixnet mode and Wireguard mode.
Wireguard nodes route data directly to the open internet. Therefore it exposes IP of operators server (VPS) to abuse complains. Before you decide to run a node with active wireguard routing, please read our Community Counsel pages containing more information and some legal content.
Wireguard mode has no exit policy right now - we are working on the implementation.
Legal support
We have been notified that a handful of nodes have been taken down by abuse reports. We created new pages with legal suggestions and email templates. Here are some useful points on legal support:
- Here is the first version of a response template tailored for Nym operators.
Dear <ISP>:
Thank you for forwarding me the notice you received from <COPYRIGHT_CLAIMANT> regarding <CONTENT>. I would like to assure you that I am not hosting the claimed infringing materials, and I believe that the notice is likely based upon misunderstandings about the law and about some of the software I run. I believe that the Digital Millennium Copyright Act's ("DMCA") safe harbor provisions likely protect you from liability arising from this complaint.
As you know, the DMCA creates four "safe harbors" for service providers (such as ISPs) to protect them from copyright liability for the acts of their users, when the service provider fulfill certain requirements. (See 17 U.S.C. 512). The requirements to meet the DMCA safe harbor provisions vary depending on the type of safe harbor claimed.
You may be familiar with the "notice and takedown" requirements of section 512(c) of the DMCA, which require a service provider respond to expeditiously to remove, or disable access to, the material that is claimed to be infringing or to be the subject of infringing activity. However, we believe that the more appropriate safe harbor provision is under section 512(a), which applies when the service provider merely acts as a conduit. In such case, there are different and less burdensome eligibility requirements, as the D.C. Circuit Court of Appeals held in RIAA v. Verizon (see https://scholar.google.com/scholar_case?case=15815830240179540527) and the Eighth Circuit Court of Appeals confirmed in RIAA v. Charter (see https://scholar.google.com/scholar_case?case=11547531128234336420).
Under DMCA 512(a), service providers like you are typically protected from damages for copyright infringement claims if you also maintain "a policy that provides for termination in appropriate circumstances of subscribers and account holders of the service provider's system or network who are repeat infringers." If you have and implement such a policy, and you otherwise qualify for the safe harbor, you should be free from fear of copyright damages.
In this case, the copyright notice you received was likely triggered by a program I run called Nym. Nym is a network software that helps users to enhance their privacy, security, and safety online.
The program does not host any content. Rather, it is part of a network of nodes on the Internet that simply pass packets among themselves before sending them to their destinations, just as any Internet intermediary does. The difference is that Nym tunnels the connections such that no intermediary can learn both the source and destination of the packets, giving users protection from nefarious snooping on network traffic. The result is that, unlike most other Internet traffic, the final IP address that the recipient receives is not the IP address of the sender. Nym protects users against hazards such as harassment, spam, and identity theft.
Nym aims to improve on technology developed by Panoramix by building a decentralized authentication and payment protocol. It will enable developers to build their own sustainable privacy-enhanced services. Panoramix is an EU-funded Horizon 2020 programme with the goal of protecting communication privacy by building a comprehensive mixnet infrastructure. This project has received funding from the European Union’s Horizon 2020 research and innovation programme under the Grant Agreement No 653497, "Privacy and Accountability in Networks via Optimized Randomized Mix-nets (Panoramix)” (For more on Nym, see https://www.nym.com/, For more on Panoramix, see https://panoramix.me/ .) I hope, as an organization committed to protecting the privacy of its customers, you'll agree that this is a valuable technology.
While the Nym node that I run may appear to be the source of material that is alleged to be infringing, I do not host that material. I do not select the material transmitted through the Nym node that I run, and I have no practical means of either identifying the source of such material or preventing its transmission. In addition, I do nothing to encourage or promote the use of the Nym network for copyright infringement or other prohibited activities. For these reasons, I am not an infringer of copyright in any materials that are transmitted through the Nym node that I run, either directly or under a theory of contributory or vicarious liability. In addition, as you are just acting as a conduit, you should continue to be protected under the DMCA 512(a) safe harbor provision without taking any further action.
Thank you for working with me on this matter. As a loyal subscriber, I appreciate your notifying me of this issue and hope that the protections of DMCA 512 put any concerns you may have to rest. If not, please contact me with any further questions.
Very truly yours,
Your customer, <YOUR_NAME/PSEUDONYM>-
We are starting Operators Legal Clinic with Alexis Roussel, every Wednesday, 14:30 UTC (60 min) in our Operator Legal Forum channel on Matrix (opens in a new tab). Come and share your findigs and questions with the rest of the operators.
-
Join Operator Legal Forum channel (opens in a new tab) and share as much as possible (like screen prints, provider, location etc).
-
Join Community legal counsel (opens in a new tab) - our collective knowledge hub. Add your findings by opening a Pull Request (opens in a new tab)
-
While we are working on a new list of more friendly providers, consider to move away from these provides as soon as possible:
- Servinga / VPS2day (AS39378)
- Frantech / Ponynet / BuyVM (AS53667)
- OVH SAS / OVHcloud (AS16276)
- Online S.A.S. / Scaleway (AS12876)
- Hetzner Online GmbH (AS24940)
- IONOS SE (AS8560)
- Psychz Networks (AS40676)
- 1337 Services GmbH / RDP.sh (AS210558)
-
Backup your nodes to have access to
.nymdirectory locally. Follow node and proxy configuration backup guides to be able to restore your node later on on another machine, without losing your delegation. -
We would like to ask operators who use reverse proxy and a domain (required for Gateways) to start using a common convention starting with
nym-exitfor their nodes URL. The entire address should have this new format:
nym-exit.<CUSTOM>.<DOMAIN>.<TLD>For example:
# for squads running multiple nodes a format can look like this:
nym-exit.ch-node1.mysquad.org
# or like this
nym-exit.3-jamaica.mysquad.org
# for operators having one node per location, the format can look like this:
nym-exit.brazil.mysquad.org
# or if operators decide to not have any custom, they can simply have this format:
nym-exit.mysquad.orgThe NYM-EXIT part in the beginning is what's important.
-
When registering a domain, check Top Level Domain (TLD) (opens in a new tab) terms and conditions. For example
.icuis a no go. Having a wrong TLD may lead to your domain being taken away from you when facing a DMCA report. -
Write a message to your provider and introduce your intention to run a Nym Node on their service
Hi,
I am reaching out to introduce myself! I am about to spin up a machine with you to run what is called a “nym node” - think of it as somewhat similar to a Tor exit node.
You can always recognize a nym node by our domain names: nym-exit
Nym node runners are a decentralized community all over the world. We provide secure internet traffic routing services to ordinary people and businesses via the Nym platform and NymVPN app.
The Nym platform implements strict encryption and security standards, which also means I simply relay traffic and do not know the end-destination nor its content.
The Nym traffic pattern is somewhat unique, as we route traffic using the “sphinx” packet format (again, think onion routing), which makes all traffic look uniform. I’d like to ensure this unique traffic pattern doesn’t raise any flags or issues with you! See https://nym.com/ for more details.
Feel free to ask any questions.
Many thanks,
<YOUR_NAME/PSEUDONYM>- New page with templates for VPS provider
Delegation Program
If you are interested to sign up to delegation program que, message Merve on Element for the time being as we are working on CRM upgrade. We review nodes dynamically and delegate to new ones once a month. New operators interested to join DP must follow the rules specified here (opens in a new tab), run one of two latest binary version and have Terms & Conditions accepted.
Note: Due to the token price we allow operators to have Operators cost 1000 NYM, the profit margin maximum remains 20%.
Delegation and undelegation in January
Delegated to all these nodes:
AMnDNd1Xgw7Em9R5vehP7r12ZNWUZ3jmitDHya6gpvGR
DLkKyYcA5feq43rqZdx6nJBNZvQsdX7kb2f1f6ED4cs2
26ZmTxTVBKHZg8MTKwypHkXZVJhDC7QHuv3BdsyRyTuk
5ZWdDN9pQ18vYkYYs5ZERh4P4JLtMiijscZ6FvwSfVxR
3uBgUJR393acoCRysu6SiLsximiwAMM85QFxq9WD8puC
5rXcNe2a44vXisK3uqLHCzpzvEwcnsijDMU7hg4fcYk8
nuMerN7ahqsptK8zDUZhnxMyDqePza8vWDf8k171EEs
86cNnnRxNpGdEtSX9UP1GpT6xrNvNuxFdHNkZcK7pAJg
9ngFADaYpT54F9i8iYFZLYR7SB7hrubsPArwpqe1RXQb
FQBbq1crAkCrjVBnEN85VqgZgGRMLJV65NJk8bPADdw
FUH3E3dghXjC9hdt3jeAhSsxwozsw1yzBXkoaFqkL4ci
5wF5wN7T2UuSsiUcQyL77NwdnXwAXxFttpZ1dR1nu4kR
4pVq4QSCcq4zNCnBNCfyugPjVhVyGDCBDSW5rghg8oZS
8XW1WWN1PuuAYz2TXQ9iWRekMFEJXjdEq4asMyE2qCCN
CxgjcTTAnRJzDxMbqtX73vEbWwLQmVoW8zS8RZEicgfT
7fwyXd4Cmh92d4piEPHmdFm1Wz1QCFQDf6bnDGNT3M6PUndelegated from 8 nodes for not meeting the rules (being offline):
# Gateways
DLxLKsd3LTnfudSSmHanPaZACsh1x4MGEzfJS4jQibir
DiciBkjHovXzTDE2EFJKPNj3TGw2oQjr7HPSas2YQPiQ
ADjpymCgjFsE5m7YvnZFxLMscg85dCUUesR5g8yN3Mzz
C9dEABjtFRMD1x4ZnbqnsELGJgutT73bPCfYzqBe7sHB
# Mixnodes
2FGgY5zWq6JP1BvpnLPbedWRYYAZELFCT9rMybNhnxpo
4nKkwPSbkbtkw3yrRKQVAVdviNgFgcNskgcSGdT2Sucy
DjY3T7n6VoHGcETMnmtZKmUU7NZP6AhCs8CoRsSSbViC
FAKhiQ8nW5sAWAxks1WB8u1MAWsapToCSE3KmF9LuGRQUndelegated due to high saturation:
5omopSZy59UyNPpx9P97vjBnN6PwPw9x5MVUx5kuNaXtService Grant Program v2
Aside from delegating on top of nodes, Nym runs a Service Grant Program (SGP) to support Exit Gateway operators before they will be rewarded by collecting zk-nym tickets from users subscription. Operators included in SGP are long term active community members with the highest requirements on the technical setup and upgrading pace. We are about to start a second iteration of SGP very soon (SGPv2). The final slots and locations are yet to be concluded. Priority to participate in SGPv2 will be given to the current operators in SGP. Based on the number of slots, we will then determine how many more operators can sign up.
Rules of SGPv2
We will share more info soon in the channels. The rules are not set in stone and could potentially be altered or updated in the future! Do not purchase new servers neither migrate your nodes just yet.
As we finalising last details of "Project Smoosh", where one binary - nym-node - can run as an entry-gateway, mixnode or exit-gateway in Mixnet mode as well as entry-gateway or exit-gateway in Wireguard mode, we plan to step up the game. SGPv2 grants will be higher if operators can meet new requirements.
Minimum Specs & Requirements
These are minimum requirements to become a part of SGPv2. We aim to have nodes on dedicated servers, with exceptions for much stronger VPS to meet the needed criteria while sharing server with other users.
nym-node - dedicated server
| Hardware | Minimum Specification |
|---|---|
| Type of server | Dedicated or bare metal |
| CPU Cores | 4 |
| Memory | 8-16 GB RAM |
| Storage | 50 GB (preferably 80 GB) |
| Connectivity | IPv4, IPv6, TCP/IP, UDP |
| Bandwidth | Unmetered if possible, or > 40Tb |
| Port speed | 1Gbps |
- Exit Gateways only
- Terms & Conditions accepted
- Nodes are bonded as
nym-nodenot as a legacy node - Only
Latestbinary version is accepted to enter the program - Timely upgrades without direct message notifications: Only
Latestversion and the two preceding are accepted to stay in the program - Dedicated (or bare metal) machine is to ensure that the numbers above are dedicated for
nym-nodeoperation - Unmetered bandwidth is to ensure smooth user experience without data allowance limitation - 40Tb is a minimum for locations where unlimited bandwidth is not an option.
- 1Gbps is an expected speed of Nym network in order to meet expectations of NymVPN users
- Squads operating more than 2 nodes are expected to run larger servers and divide them for multiple nodes - We will share a how-to guide soon
- Operators need to run reverse proxy with landing page URL starting with
nym-exitand Web Secure Socket configuration - Operators must write their providers upfront that they will run a Nym Exit Gateway on their servers, using this template
- If a node remains offline for more than 5 days for any reason, including abuse reports, and the operator doesn't resolve it neither doesn't communicate the blockers, they will be removed from the program
Operators interested in joining SGPv2 can start by searching for servers that meet the above criteria, where they may eventually migrate their nodes, and then share their findings by submitting a form which will be shared shortly. Do not buy a new server, neither migrate a node just yet! We will be first reaching to the current participants of Service Grant Program. Everything will be announced, sending DMs to devrel will not speed up the process!
Features
-
build(deps): bump criterion from
0.4.0to0.5.1(opens in a new tab): Bumps criterion (opens in a new tab) from0.4.0to0.5.1. -
build(deps): bump http from
1.1.0to1.2.0(opens in a new tab): Bumps http (opens in a new tab) from1.1.0to1.2.0. -
http-api-client: deduplicate code (opens in a new tab): After adding PATCH support in #5260 (opens in a new tab), it's now time to de-duplicate some of the code -
nym topology revamp (opens in a new tab): This PR changes the internals of the
NymTopologyto blur the lines between explicit mixnodes and gateways so that what used to be considered a "mixnode" could be a valid egress point of the network.NymTopologyis no longer divided intoBTreeMap<MixLayer, Vec<mix::Node>>andVec<gateway::Node>. instead there's information about the current rewarded set (to support future VRF work) and a simple map ofHashMap<NodeId, RoutingNode>. The new features are mostly controlled via 2 new flags/config values:use_extended_topologythat tells the client to retrieve all network nodes rather than the ones that got assigned "active" mixnode role (or support being a gateway)ignore_egress_epoch_rolethat tells the client it's fine to construct egress packets to nodes that are not assigned entry or exit gateway role
-
Move tun constants to network defaults (opens in a new tab):
- Regression Testing:
- Verified no issues arose when running tests for the affected files.
- Tested TUN behaviour with new nym-nodes in the hu branch.
Results:
- No bugs detected.
- Tunnels are functioning as expected, with traffic routing and IP generation working seamlessly.
-
Add dependabot assignes for the root cargo ecosystem (opens in a new tab)
-
build(deps): bump the patch-updates group across 1 directory with 35 updates (opens in a new tab): Bumps the
patch-updatesgroup with 33 updates -
Periodically remove stale gateway messages (opens in a new tab): This PR introduces a simple task that removes gateway messages that haven't been retrieved in (by default) 24h.
Automation Script for Data Cleanup Validation
Test Objective: Validate that the stale message cleanup mechanism in the database correctly removes records older than the configured threshold (24 hours).
Test Setup:
- Environment:
- SQLite database
- Bash script: used to insert data.
Steps Performed:
- Ran the insert_data.sh script to populate the database with test data:
- Recent records inserted successfully.
- Verified the database content post-insertion: sqlite3 clients.sqlite "SELECT * FROM message_store;"
- Confirmed that all 20 records (10 recent + 10 stale) were present.
- Allowed the system to run for 24 hours to trigger the cleanup mechanism.
- Queried the database again after 24 hours: sqlite3 gateway_storage.db "SELECT * FROM message_store;"
Expected Result:
- All stale records (older than 24 hours) should be removed.
- Recent records should remain in the database. Actual Result:
- Query after 24 hours showed only the 10 recent records.
- All 10 stale records were successfully removed.
- Use expect in geodata test to give error message on failure (opens in a new tab): Keep hitting this error on CI, from what I think is network hickup. But it's hard to tell form the log since the error is swallowed. Explicitly unwrap the result so we get a more detailed error output.
Quick Code Review
Summary
- CI Workflow: Adjusted paths to optimise build triggers, avoiding unnecessary CI runs while ensuring coverage for key directories
- Geolocation Test: Improved error handling by replacing assertions with
.expectfor clearer debugging in API regression tests
Conclusion
Regression testing confirms everything works as intended. Approved.
-
CancellationToken-based shutdowns (opens in a new tab): This PR introduces scaffolding for usingCancellationTokenandTaskTrackerfor our graceful shutdowns rather than the existingTaskClientandTaskManager. -
Introduce
/loadendpoint for self-reported quantised Nym Node load (opens in a new tab): This PR introduces a new/loadendpoint on aNymNodeto return its current load. It returns the following data:
pub struct NodeLoad {
pub total: Load,
pub machine: Load,
pub network: Load,
}Where Load is quantised into the following buckets / tiers:
pub enum Load {
Negligible, // 0 - 0.1
Low, // 0.1 - 0.3
Medium, // 0.3 - 0.6
High, // 0.6 - 0.8
VeryHigh, // 0.8 - 0.95
AtCapacity, // >= 0.95
}/load endpointThe actual values forNodeLoad are determined as follows:
- For network we approximate current rx/tx rates on all
ethinterfaces and scale them to the range of 0-1Gbps (for this initial iteration we assume the maximum network speed is 1Gbps which would be treated as fully saturated). So for example, if the node is sending at 0.5Gbps, it would get aLoadof 0.5 and thus value ofLoad::Medium, 0.9Gbps would getLoadof 0.9 and value ofLoad::VeryHigh, etc. we take the bigger value between rx and tx - For machine load there's a bit more logic in there:
- Firstly we determine what I call a "base load" of the machine. we do this by taking the average load from the last 5min (via
getloadavg) and dividing it by the number of CPUs in the machine. For example if the average load of the machine in the last 5min was1.23and it has 2 CPUs, then it'sLoadwould beLoad::High(1.23 / 2 = 0.615) - However, whilst CPU utilisation is one of the most important factors, it does not tell the whole story. I tried to also take memory/swap utilisation into consideration (whilst not making it the main factor)
- Thus we calculate two additional auxiliary
Loadvalues, for memory usage and swap usage, i.e.:used_memory / total_memoryandused_swap / total_swaprespectively. - Then we check whether either of the
MemoryLoadorSwapLoadis bigger than the current baseLoadof the machine we have determined, if so, it's increased by one tier / bucket. For example, say the current machine load isLoad::Low, but the memory usage is at 90% (Load::VeryHigh). that would result in the reportedLoadbeing bumped up toLoad::Mediuminstead. The same logic applies with swap load, however, only if the total swap > 1GB. this is to prevent weird edge cases where the machine has hardly any swap. - Finally, the
.totalLoaduses the same "tier bumping" behaviour using the.totaland.networkloads, i.e.if network > machine, thentotal = machine + 1. for example ifmachineLoadisLoad::Low, butnetworkLoadisLoad::Medium, then thetotalLoadis set toLoad::Mediuminstead.
- Firstly we determine what I call a "base load" of the machine. we do this by taking the average load from the last 5min (via
-
Bump the
patch-updatesgroup with 8 updates (opens in a new tab) -
Updated
cosmrsandtendermint-rpcto their most recent versions (opens in a new tab) -
Bump mikefarah/yq from
4.44.6to4.45.1(opens in a new tab) -
Update
indexed_db_futures(opens in a new tab): Updates theindexed_db_futuresdependency to stop relying on the fork. -
Refresh wasm sdk (opens in a new tab): This PR refreshes the wasm clients to make them usable in the current network
-
Client gateway selection (opens in a new tab): Changed how gateway is selected.
- For init the target gateway can't support mixing
- For egress, unless
ignore_epoch_rolesis specified, the gateway can't be currently assigned to a mixing layer. But it can be standby or inactive
-
Exposed
NymApiClientmethod for obtaining node performance history (opens in a new tab) -
Bind to
[::]onnym-nodefor both IP versions (opens in a new tab)
IPv4 Configuration and Migration Testing
Testing Steps:
- Initiated and ran a nym-node with version 1.3.1 on an IPv4-only machine, then updated it to the new 'hu', 1.4.0 version.
- Initiated and ran a new nym-node with 'hu', 1.4.0 always on a machine with only IPv4.
- Initiated and ran a new nym-node with 'hu', 1.4.0 on a machine with both IPv4 and IPv6 for regression testing.
Results:
- No functional issues during version updates.
- Logged message on all versions: "no registered client for destination: ff02::2"
Status: Pass
-
Handle ecash network errors differently (opens in a new tab): For errors that could be caused by network problems, we should mark the ticket as still pending, not as bad. This won't fix the underlying problem, but should not assume anymore that the client is the culprit and penalise its bandwidth quota.
-
Make client ignore dual mode nodes by default (opens in a new tab)
Testing Steps:
- Ensured a client is able to select a node which aside from a gateway, can also act as a mixnode
- Verified 'ignore_epoch_roles' is the default mode
- note; this is most likely not going to be a permanent solution
Results:
- Clients and topology are behaving correctly
Status: Pass
Bugfix
- Remove unnecessary arguments for nym-api swagger endpoints (opens in a new tab)
- Fixed sql migration for adding default message timestamp (opens in a new tab)
- Terminate mixnet socket listener on shutdown (opens in a new tab)
- Correctly handle ingore epoch roles flag (opens in a new tab)
v2025.1-reeses
- Release Binaries (opens in a new tab)
nym-nodeversion1.3.1
nym-node
Binary Name: nym-node
Build Timestamp: 2025-01-16T11:54:17.079662337Z
Build Version: 1.3.1
Commit SHA: 5ab164d229f85bd2dd27ec6e38292c281df2f678
Commit Date: 2025-01-16T12:51:53.000000000+01:00
Commit Branch: HEAD
rustc Version: 1.84.0
rustc Channel: stable
cargo Profile: releaseOperators Updates & Tools
From nym-node v1.3.0 operators can choose multiple functionalities for their nym-node binary (flagged as --mode).
However, the clients are yet to be developed to be able to make a proper selection for multi-mode nodes and therefore we ask operators to sign only one functionality to --mode option at a time. Please chose out of: mixnode or entry-gateway or exit-gateway.
We are developing a design where operators can enable multiple modes, and let the Nym API to position the node according the network's needs in the beginning of each epoch.
- Node functionality info updated
- Fund your
nym-nodeinbuilt Nyx account to prepare for gateway ticket rewarding config.tomlchanges:- Replaced
modewithmodesto allow setting the node to run with say,entry+mixnoderoles simultaneously - Added
maximum_forward_packet_delaytomixnet.debugsection - Moved
verlocsection frommixnode.verlocto top level - Removed
mixnodesection - Removed
entry_gatewaysection togateway_tasks - Moved
authenticatorsection fromgateway_tasks(entry_gateway) toservice_providers(exit_gateway) - Renamed
exit_gatewaysection toservice_providers - Moved top level
authenticatorsection toservice_providersso that it'd live alongside NR and IPR - Added general
debugsection - Added
metricssection
- Replaced
- All documentation migrated to a new URL nym.com/docs (opens in a new tab) alongside the rebranding of Nym organisation.
- Updated network architecture diagrams (opens in a new tab)
- New blow-by-blow mixnet traffic flow (opens in a new tab) section
- Winter Nym Squad League started (opens in a new tab)
- From this release onward (New Year) Operators Updates & Tools will be on top of each release changelog followed by features, cryptography and bugfix parts.
- All 2024 release notes were moved to the bottom section called Archived changelog
Features
- build(deps): bump micromatch from
4.0.4to4.0.8in/testnet-faucet(opens in a new tab): Bumps micromatch (opens in a new tab) from4.0.4to4.0.8. - Move NS client to separate package under NS API (opens in a new tab):
- Moving NS API client code to separate package outside NS Agent makes the code cleaner & more modular
- NS agent now imports NS API client that it uses
- No functionality change in NS API or NS agent
- Introduced initial internal commands for nym-cli: ecash key and request generation (opens in a new tab)
- NS API - Gateway stats scraping (opens in a new tab): This PR adds a metrics scraper that fetches metrics from the
metrics/sessionsendpoint on gateway. The entries are stored and served on the API for one year - Remove explorer dependency (opens in a new tab)
- Hopefully final steps of the smoosh™️ (opens in a new tab): this PR is a bit more extensive than initially planned because of all the spaghetti that had to be untangled to make it all happen. The general idea is that now it's possible to run your node simultaneously in multiple modes. for example
mixnode+entryorentry+exit, etc. The modes do the following:mixnode: allows the node to handle forward sphinx packetsentry-gateway: allows the node to accepts websocket connections from incoming clients and to handle final hop sphinx packetsexit-gateway: allows the node to handle final hop sphinx packets as well as starts NR and IPR service providers Furthermore, if node runs withwireguardenabled, it will start localauthenticatorservice provider which will also implicitly enable final hop packet handling regardless of the underlying mode. There are also various of other smaller (and bigger) changes:- Upon receiving a forward packet, its delay is now clamped so that one could not dos the node by asking it to delay it for, for example, a year
- As mentioned above, node can now run in multiple modes at the same time,
/metrics/mixingendpoint got deprecated (it still provides the same information, however) and might be removed in future release- Introduced
/metrics/packet-statsendpoint that provides more extensive information about packets received/sent - It is now possible to control whether the node should log its statistics to console
- The console logs are also updated with the current packet rates
- All nodes now run the "verloc" protocol and measure every other node on the network
- Metrics got revamped and unified:
- All running metrics are stored in a single
NymNodeMetricsstruct - There exists a
MetricsAggregatorthat listens to any metrics events that might require additional processing - Any new metrics event types can be easily added by registering a new handler via
register_handler. the type must implementMetricsHandlertrait and use unique variant ofMetricsEventenum. for exampleGatewaySessionStatsHandler. It is, however, possible to have opaque handlers, such as the already implementedLegacyMixingStatsUpdaterandMixnetMetricsCleaner - Everything in
mixnodedirectory has been removed because there was nothing really left there. The mixing socket listener was unified innym-nodeand similarlyverlocwas also moved there gatewaydirectory was similarly reduced in size. Now it also creates appropriate tasks as opposed to the whole gateway process. eventually it might also be further stripped, but today is not that day.- Removed the generic parameter on the
GatewayStorageto simplify all the generics down the stack. it wasn't used anyway
CLI:
- Added
--modesargument to specify all node modes with a single command (orenvvariable). for example:--modes="mixnode,entry". Can't be used alongside--modes - Extended
--modeargument to allow specifying it multiple times, for example:--mode mixnode --mode entry. can't be used alongside--mode
Config changes:
- Replaced
modewithmodesto allow setting the node to run with say,entry+mixnoderoles simultaneously - Added
maximum_forward_packet_delaytomixnet.debugsection - Moved
verlocsection frommixnode.verlocto top level - Removed
mixnodesection - Removed
entry_gatewaysection togateway_tasks - Moved
authenticatorsection fromgateway_tasks(entry_gateway) toservice_providers(exit_gateway) - Renamed
exit_gatewaysection toservice_providers - Moved top level
authenticatorsection toservice_providersso that it'd live alongside NR and IPR - Added general
debugsection - Added
metricssection - Better date serialization (opens in a new tab): Proper date serialization for NS API session stats
- Restore Location fields (opens in a new tab): restore
latitudeandlongitudefields - Derive serialize for UserAgent (opens in a new tab)
- Change sqlite journal mode to WAL (opens in a new tab)
- Shipping raw metrics to PG (opens in a new tab)
- Extend raw ws fd for gateway client (opens in a new tab)
- Add fd callback to client core (opens in a new tab)
- TicketType derive Hash and Eq (opens in a new tab): It's useful to keep
TicketTypein maps, which requireHash. Also deriveEqsince it's useful. - Extend swagger docs (opens in a new tab)
- Add FromStr impl for UserAgent (opens in a new tab): Add
FromStrimplementation forUserAgentto make it easier to pass in custom user agent in vpn clients as a CLI argument. - Remove unneeded async function annotation (opens in a new tab)
- Add control messages to
GatewayTransciver(opens in a new tab)
Review and Testing: Forget Me Implementation
- Validated the encryption and delivery of
ForgetMecontrol messages to the gateway
Testing: MixTrafficController Integration
- Verified that the
MixTrafficControllerinvokesForgetMelogic correctly during shutdown - Tested behaviour for gateway transceiver failures while sending control messages
Testing: Gateway Storage Updates
- Confirmed successful deletion of client data (e.g., inbox messages, bandwidth allocations) from persistent storage
- Add conversion unit tests for auth msg (opens in a new tab)
- Update TS bindings (opens in a new tab)
- Removed legacy socks5 listener (opens in a new tab)
- Add PATCH support to
nym-http-api-client(opens in a new tab): AddPATCHsupport tonym-http-api-clientcrate - Wireguard metrics (opens in a new tab): With this PR on each peer controller update the following global metrics information are also updated:
- total bytes tx
- total bytes rx
- current active peers
- total peers registered
- The former two are exposed with REST endpoints
/api/v1/metrics/wireguard-stats, while the rest will be accessible via prometheus (soon ™️ ). The wireguard stats are also logged to the console (assuming they're non-zero)
- Add close to credential storage (opens in a new tab): Add close method to credential storage
- Review File:
common/credential-storage/src/backends/sqlite.rs
- Verified addition of
closemethod for the SQLite backend
- Review File:
common/credential-storage/src/ephemeral_storage.rs
- Confirmed addition of
closemethod for ephemeral storage with no action required
- Review File:
common/credential-storage/src/persistent_storage/mod.rs
- Ensured
closemethod integration for persistent storage
- Review File:
common/credential-storage/src/storage.rs
- Verified updates to the
Storagetrait to includecloseandcleanup_expiredmethods
- Review File:
common/network-defaults/src/constants.rs
- Confirmed updated
mixnet_vpnconstants were added.
- Review File:
service-providers/ip-packet-router/src/constants.rs
- Checked replacement of legacy
TUN_*constants with newmixnet_vpnconstants. - Validated alignment of routing traffic configurations.
- Review File:
service-providers/ip-packet-router/src/ip_packet_router.rs
- Ensured new
nym_network_defaults::constants::mixnet_vpnconstants replaced old references. - Verified
TunDeviceConfigconsistency.
- Review File:
service-providers/ip-packet-router/src/util/generate_new_ip.rs
- Confirmed substitution of
TUN_DEVICE_*constants withNYM_TUN_DEVICE_*constants. - Tested functionality for generating random IPs within subnet.
- Expand
nym-nodeprometheus metrics (opens in a new tab): This PR undusts the/api/v1/metrics/prometheusand introduces the following 37 new data points:
-
mixnet:
-
ingress:
-
nym_node_mixnet_ingress_forward_hop_packets_received -
nym_node_mixnet_ingress_final_hop_packets_received -
nym_node_mixnet_ingress_malformed_packets_received -
nym_node_mixnet_ingress_excessive_delay_packets -
nym_node_mixnet_ingress_forward_hop_packets_dropped -
nym_node_mixnet_ingress_final_hop_packets_dropped -
nym_node_mixnet_ingress_forward_hop_packets_received_rate -
nym_node_mixnet_ingress_final_hop_packets_received_rate -
nym_node_mixnet_ingress_malformed_packets_received_rate -
nym_node_mixnet_ingress_excessive_delay_packets_rate -
nym_node_mixnet_ingress_forward_hop_packets_dropped_rate -
nym_node_mixnet_ingress_final_hop_packets_dropped_rate
-
-
egress:
-
nym_node_mixnet_egress_stored_on_disk_final_hop_packets -
nym_node_mixnet_egress_forward_hop_packets_sent -
nym_node_mixnet_egress_ack_packets_sent -
nym_node_mixnet_egress_forward_hop_packets_dropped -
nym_node_mixnet_egress_forward_hop_packets_sent_rate -
nym_node_mixnet_egress_ack_packets_sent_rate -
nym_node_mixnet_egress_forward_hop_packets_dropped_rate
-
-
-
client sessions
nym_node_entry_client_sessions_unique_usersnym_node_entry_client_sessions_sessions_startednym_node_entry_client_sessions_finished_sessionsnym_node_entry_client_sessions_durations_{TYP}(histogram), for examplenym_node_entry_client_sessions_durations_vpn
-
wireguard:
-
nym_node_wireguard_bytes_rx -
nym_node_wireguard_bytes_tx -
nym_node_wireguard_bytes_total_peers -
nym_node_wireguard_bytes_active_peers -
nym_node_wireguard_bytes_rx_rate -
nym_node_wireguard_bytes_tx_rate
-
-
network
nym_node_network_active_ingress_mixnet_connectionsnym_node_network_active_ingress_web_socket_connectionsnym_node_network_active_egress_mixnet_connections
-
process
nym_node_process_forward_hop_packets_being_delayednym_node_process_packet_forwarder_queue_sizenym_node_process_topology_query_resolution_latency(histogram)nym_node_process_final_hop_packets_pending_deliverynym_node_process_forward_hop_packets_pending_delivery
- Amend 250gb limit (opens in a new tab): Change bandwidth cap to 250gb
- Warn users if node is run in exit mode only (opens in a new tab): Throws a warning if node is run in "exit" mode only as by default, this will NOT enable entry capabilities, i.e. opening the websocket. thus making it ineligible for rewarded set selection (and rewards)
- Reduce log severity for number of packets being delayed (opens in a new tab)
- Apply 1.84 linter suggestions (opens in a new tab)
- Readjusted --mode behaviour to fix the regression (opens in a new tab)
- Legacy alert (opens in a new tab): alert moved into
navcomponents
Bugfix
- Fix overflow (opens in a new tab)
- Fix overflow again (opens in a new tab)
- Make sure to update timestamp of last batch verification to prevent double redemption (opens in a new tab)
- Make sure to apply gateway score filtering when choosing initial node (opens in a new tab)
- Fixed client session histogram buckets (opens in a new tab)
- Contract version assignment (opens in a new tab): This PR fixes updates to current nym-node version as well as introduces migration to fix the existing state of the mainnet contract
- Make sure refresh data key matches bond info (opens in a new tab): This is to forbid operators from reusing the same underlying identity key for multiple nodes by overwriting the describe data. the reported key has to always match what the node has bonded with (and the contract enforces uniqueness)
Archived Changelog
To allow reading through older changelogs, we store them below sorted by years.
v2024.14-crunch-patched
Patch for v2024.14-crunch release. Fixes an issue (opens in a new tab) to allow only one private IP pair & compatibility issues between nym-nodes and older clients.
- Release binaries (opens in a new tab)
nym-nodeversion1.2.1
nym-node
Binary Name: nym-node
Build Timestamp: 2024-12-18T10:18:42.978852430Z
Build Version: 1.2.1
Commit SHA: 8d5a41a790e96ae5e821964865affaa7d3343eab
Commit Date: 2024-12-18T11:07:49.000000000+01:00
Commit Branch: HEAD
rustc Version: 1.83.0
rustc Channel: stable
cargo Profile: releasev2024.14-crunch
- Release binaries (opens in a new tab)
nym-nodeversion1.2.0- Operators updates and tools
- Github CHANGELOG.md (opens in a new tab)
nym-node
Binary Name: nym-node
Build Timestamp: 2024-12-11T13:49:11.974104790Z
Build Version: 1.2.0
Commit SHA: a491e6a71a8cf862d77defd740a4ee8d65d8292a
Commit Date: 2024-12-11T10:28:47.000000000+01:00
Commit Branch: HEAD
rustc Version: 1.83.0
rustc Channel: stable
cargo Profile: releaseFeatures
-
Bump elliptic from
6.5.4to6.5.7in /testnet-faucet (opens in a new tab): Bumps elliptic (opens in a new tab) from6.5.4to6.5.7. -
build(deps): bump micromatch from
4.0.4to4.0.8in /nym-wallet/webdriver (opens in a new tab): Bumps micromatch (opens in a new tab) from4.0.4to4.0.8. -
build(deps): bump axios from 1.6.0 to 1.7.5 in /nym-api/tests (opens in a new tab) Bumps axios (opens in a new tab) from 1.6.0 to 1.7.5.
-
Sync code with
.envin build.rs (opens in a new tab): Keepdotenvfile always up to date -
build(deps): bump lazy_static from
1.4.0to1.5.0(opens in a new tab): Bumps lazy_static (opens in a new tab) from1.4.0to1.5.0. -
Create TaskStatusEvent trait instead of piggybacking on Error (opens in a new tab)
-
build(deps): bump once_cell from
1.19.0to1.20.2(opens in a new tab): Bumpsonce_cell(opens in a new tab) from1.19.0to1.20.2 -
Bump the patch-updates group across 1 directory with 10 updates (opens in a new tab): Bumps the patch-updates group with 9 updates in the / directory:
| Package | From | To |
|---|---|---|
| anyhow (opens in a new tab) | 1.0.89 | 1.0.90 |
| clap (opens in a new tab) | 4.5.18 | 4.5.20 |
| clap_complete (opens in a new tab) | 4.5.29 | 4.5.33 |
| pin-project (opens in a new tab) | 1.1.5 | 1.1.6 |
| serde (opens in a new tab) | 1.0.210 | 1.0.211 |
| serde_json (opens in a new tab) | 1.0.128 | 1.0.132 |
| wasm-bindgen (opens in a new tab) | 0.2.93 | 0.2.95 |
| wasm-bindgen-futures (opens in a new tab) | 0.4.43 | 0.4.45 |
| web-sys (opens in a new tab) | 0.3.70 | 0.3.72 |
Updates anyhow | 1.0.89 | 1.0.90 |
-
[Product Data] Introduce data persistence on gateways (opens in a new tab): This PR builds on top of #4974 (opens in a new tab), not changing the behavior of the data collection, but persisting them in a sqlite database so they can be kept across restarts and crashes. It also leave the door open for other stats module to use that storage if needed. Here are some points of interest:
- New
gateway_stats_storage(opens in a new tab) crate - Config migration (opens in a new tab) resulting from the added database.
- Resulting changes in the
statistics(opens in a new tab) module to account the new storage system
- New
-
Integrate nym-credential-proxy into workspace (opens in a new tab): Integrate
nym-credential-proxyinto the main workspace -
Node Status API (opens in a new tab): merging a long-diverged feature branch - all commits here were their own merge requests
-
[Product Data] Better unique user count on gateways (opens in a new tab): To avoid double counting clients across gateways, we add a user ID to the gateway session data.
-
chore: ecash contract migration to remove unused 'redemption_gateway_share' (opens in a new tab)
-
[Product Data] Client-side stats collection (opens in a new tab): The goal is to anonymously gather stats from nym-clients. These stats will be sent through the mixnet to a Nym run service provider that will gather them. This PR sets the scene to send stats in a mixnet message to an address. The address can be set when the client is created. Current stats include some infos on sent packets along with platform information. If a receiving address is set, the client will send a mixnet packet every 5min to this address. Otherwise, nothing happens and the client runs as usual.
-
Send mixnet packet stats using task client (opens in a new tab)
-
Add granular log on nym-node (opens in a new tab) and make use of it for
defguard_wireguard_rsbig info logs -
Rewarding for ticketbook issuance (opens in a new tab): Revamps the current validator rewarder to allow for rewards for issuing the zk-nym ticketbooks.
-
[Product Data] Add stats reporting configuration in client config (opens in a new tab): Adds the stats reporting address to client configs. It can be set in the config file, as a CLI argument and as an env var in a
.envfile. As the stats reporting config in now in theDebugConfig, theStatsReportingConfigis no longer required, making the propagation of these changes more readable -
config score (opens in a new tab): introduces a concept of a
config_scoreto a nym node which influences performance and thus rewarding amounts and chances of being in the rewarded set. Currently it's influenced by the following factors:- Accepting terms and conditions (not accepted: 0)
- Exposing self-described API (not exposed: 0)
- Running "nym-node" binary (legacy binary: 0)
- Number of versions behind the core (
score = 0.995 ^ (X * versions_behind ^ 1.65)) - The old performance is now treated as
routing_score - the "new" performance =
routing_score * config_score
-
Add Dockerfile and add env vars for clap arguments (opens in a new tab)
-
Aadd GH workflow for nym-validator-rewarder (opens in a new tab)
-
[Product data] Data consumption with ecash ticket (opens in a new tab): Send an event each time an ecash ticket get successfully spent. This allows to approximate how much data each client is using.
-
[Product Data] Config deserialization bug fix (opens in a new tab): Fixes a bug where a
Nonevalue was serialized into an empty string, and incorrectly deserialized into aSomevariant. -
NS Agent auth with NS API (opens in a new tab): NS Agent authenticates with key that was registered with NS API
- Added flag to Agent to generate keypairs
- Agent requests are signed by agent
- Server-side requests are checked for authentication
-
Removed ci-nym-api-tests.yml which was running outdated (and broken) tests (opens in a new tab)
-
[Product Data] Set up country reporting from vpn-client (opens in a new tab): Add the ability to report exit country, along with a small refactoring of a module.
-
chore: remove standalone legacy mixnode/gateway binaries (opens in a new tab)
-
Update
serde_json_pathdue to compilation issue (opens in a new tab) -
Add version to clientStatsReport (opens in a new tab): Add a
kindandapi_versionfield forClientStatsReport -
Start session collection for exit gateways (opens in a new tab): Apparently, exit gateways are also entry gateways so we need to start session stats for them as well
-
build(deps): bump mikefarah/yq from
4.44.3to4.44.5(opens in a new tab): Bumps mikefarah/yq (opens in a new tab) from4.44.3to4.44.5. -
build(deps): bump cross-spawn from
7.0.3to7.0.6in /testnet-faucet (opens in a new tab): Bumps cross-spawn (opens in a new tab) from7.0.3to7.0.6. -
Add export_to_env to NymNetworkDetails (opens in a new tab): In
nym-vpn-corewe've started to read the network environment from a json file and then try to pass aroundNymNetworkDetailsdirectly instead of relying on the exported environment. However we still need to bridge with old code so we need to export the network details instance to the environment. -
Add support for DELETE to nym-http-api-client (opens in a new tab): Add delete support to
http-api-client -
Add derive_extended_private_key to DirectSecp256k1HdWallet (opens in a new tab): Add
derive_extended_private_keytoDirectSectp256k1HdWalletto support seeding ecash keys -
Move two minor jobs to free tier github hosted runners (opens in a new tab): In an attempt to easy the load on the self-hosted runners, move two minor workflows over to GH hosted free tier runners.
-
Remove peers with no allowed ip from storage (opens in a new tab)
-
Add indexes to monitor run and testing route (opens in a new tab)
-
Add
monitor_runand testing_route indexes (opens in a new tab) -
explorer-api: add nym node endpoints + UI to show nym-nodes and account balances (opens in a new tab): Explorer API:-
Existing endpoints stay identical
-
Adds new endpoints to get:
-
nym-nodes(list + by id) -
account balance + delegations + rewarding + vesting
-
Explorer UI (NextJS)
- List of nym-nodes
- Remove service providers routes (Harbour Master shows these)
- Updates summary page to show nym-nodes
- Adds legacy markers to old gateway and mixnode bond lists
-
-
Add
monitor_runand testing_route indexes (opens in a new tab) -
improvement: make internal gateway clients use the same topology cache (opens in a new tab): This should result in 66% reduction in queries for topology within
nym-nodeas all the clients should rely on the same cache -
Update Security disclosure email, public key and policy (opens in a new tab)
-
adjusted config score penalty calculation (opens in a new tab)
-
Nmv2 add debug config (opens in a new tab): Adds debug config to disable poisson process, cover traffic and min performance filtering
-
introduce UNSTABLE endpoints for returning network monitor run details (opens in a new tab)
-
Don't consider legacy nodes for rewarded set selection (opens in a new tab)
-
Derive serialize for UserAgent (#5210) (opens in a new tab): Cherry-pick PR #5210 (opens in a new tab)
-
Remove any filtering on node semver (opens in a new tab): Removed any filtering on version of nodes. however, the parameters can still be passed to
nym-apiqueries to not break existing clients, but they will happily ignore them -
Further config score adjustments (opens in a new tab): I still want to add helper endpoints on
nym-apito expose some of this data. but for now, I'll let this PR bake over the weekend.
Bugfix
-
bugfix: don't send empty BankMsg in ecash contract (opens in a new tab): If ticketbook prices were to be set so low the resultant redemption would have created
BankMsgwith value of 0, that message is no longer going to be sent -
bugfix: correctly expose ecash-related data on nym-api (opens in a new tab): This PR makes fixes to ecash-related endpoints on
nym-api- global data (such as aggregated signatures and keys) are actually always available by all apis
- global data (such as aggregated signatures and keys) are actually always available by all apis
-
bugfix: use default value for verloc config when deserialising missing values (opens in a new tab)
-
bugfix: fixed nym-node config migrations (again) (opens in a new tab)
-
bugfix: added explicit openapi servers to account for route prefixes (opens in a new tab)
Operators Updates & Tools
Nym Network will now only allow nodes which migrated their node in Nym mixnet smart contract to Nym Node. All nodes which are still bonded as a legacy one (Mixnode or Gateway) in the wallet will have no chance to take part in the Rewarded set selection.
Operators taking part in Delegation program or Service Grant program must migrate their nodes latest by December 16th, 08:00 UTC.
Updates
- Version count as a part of config score has been introduced. To familiarize yourself with Nym Node operator rewards calculation, read this page.
- Nym nodes running as Exit Gateway in Service Grant program received delegation. Nym team is now delegating total of 64,800,000 NYM on top 241 Nym Nodes (137 in Mixnode mode and 104 as Gateways). Our delegation aims to incentivise committed operators who support bootstrapping of Nym network before paying users come.
- 250k NYM - Upgrading to magura in time - 2 nodes
- 300k NYM - Upgrading to magura + bonus for a quick patch upgrade - 102 nodes
- No delegation - not upgrading in time - 2 nodes
-
nym-nodehas now implemented IPv6 support for wireguard (opens in a new tab) -
network_tunnel_manager.shupdated (opens in a new tab): run the commands below to make sure
network_tunnel_manager.shThese commands can be run one by one or copy-pasted and run as a block.
mkdir $HOME/nym-binaries; \
curl -L https://raw.githubusercontent.com/nymtech/nym/refs/heads/develop/scripts/network_tunnel_manager.sh -o $HOME/nym-binaries/network_tunnel_manager.sh && \
chmod +x $HOME/nym-binaries/network_tunnel_manager.sh; \
$HOME/nym-binaries/network_tunnel_manager.sh check_nymtun_iptables ; \
$HOME/nym-binaries/network_tunnel_manager.sh remove_duplicate_rules nymtun0 ;\
$HOME/nym-binaries/network_tunnel_manager.sh remove_duplicate_rules nymwg;\
$HOME/nym-binaries/network_tunnel_manager.sh check_nymtun_iptables ; \
$HOME/nym-binaries/network_tunnel_manager.sh adjust_ip_forwarding ; \
$HOME/nym-binaries/network_tunnel_manager.sh apply_iptables_rules ; \
$HOME/nym-binaries/network_tunnel_manager.sh check_nymtun_iptables ; \
$HOME/nym-binaries/network_tunnel_manager.sh apply_iptables_rules_wg ; \
$HOME/nym-binaries/network_tunnel_manager.sh configure_dns_and_icmp_wg ; \
$HOME/nym-binaries/network_tunnel_manager.sh adjust_ip_forwarding ; \
$HOME/nym-binaries/network_tunnel_manager.sh check_ipv6_ipv4_forwarding; \
systemctl daemon-reload && service nym-node restart && journalctl -u nym-node -fThen run the jokes in a new window for control
$HOME/nym-binaries/network_tunnel_manager.sh joke_through_the_mixnet
$HOME/nym-binaries/network_tunnel_manager.sh joke_through_wg_tunnelTools
- New APIs documentation with interactive APIs generated from the OpenAPI specs of various API endpoints offered by bits of Nym infrastructure run both by Nym and community operators for both Mainnet and the Sandbox testnet.
- Nym Harbourmaster (opens in a new tab) has a new tab called
CONTRACT EXPLORERquerying data from Nym mixnet contract in real time. - Nym Explorer (opens in a new tab) is updated to read migrated nodes correctly
- New community explorer by SpectreDAO (opens in a new tab) offers Nym Network dashboard, Node overview and Account stats view functions for operators and delegators.
nym-vpncbuild and run documentation, for those who don't want to use the Nym VPN GUIs.
magura-drift
Second patch to v2024.13-magura release version.
- Release binaries (opens in a new tab)
nym-nodeversion1.1.12
nym-node
Binary Name: nym-node
Build Timestamp: 2024-11-29T13:10:51.813092288Z
Build Version: 1.1.12
Commit SHA: 4a9a5579c40ad956163ea02e01d7b53aef2ac8ef
Commit Date: 2024-11-29T14:06:32.000000000+01:00
Commit Branch: HEAD
rustc Version: 1.83.0
rustc Channel: stable
cargo Profile: release- This patch adds a peer storage manager to fix issues causing external clients to be blocked, ensuring they can successfully connect to different nodes.
v2024.13-magura-patched
- Release binaries (opens in a new tab)
nym-nodeversion1.1.11
nym-node
Binary Name: nym-node
Build Timestamp: 2024-11-22T14:30:48.067329245Z
Build Version: 1.1.11
Commit SHA: 01c7b2819ee3d328deccd303b4113ff415d7e276
Commit Date: 2024-11-22T10:50:59.000000000+01:00
Commit Branch: HEAD
rustc Version: 1.82.0
rustc Channel: stable
cargo Profile: releaseAfter changes coming along with v2024.13-magura (nym-node v1.1.10), Nym Explorer is no longer picking all values correctly. Instead of fixing this outdated explorer, we are working on a new one, coming out soon.
Nym Harbourmaster (opens in a new tab) has cache of 90min, expect your values to be updated with delay. We are aware of some issues with Nym Harbourmaster and working hard to resolve them in the upcoming explorer v2. To check your routing values in real time, you can use nym-gateway-probe.
Operators Updates & Tools
-
Updated
network_tunnel_manager.sh(opens in a new tab) (moved to our monorepo) helps operators to configure their IP tables rules fornymtunandwireguardrouting. -
Please re-run routing configuration steps to update your routing settings.
-
We found out that some operators have a wrong value for wireguard IP. Follow these steps to ensure your value is set to
10.1.0.1(default on new nodes):
1. Open your node config file:
nano $HOME/.nym/nym-nodes/<ID>/config/config.toml
# change <ID> for your local nym moniker for example:
# nano $HOME/.nym/nym-nodes/default-nym-node/config/config.toml2. Control or change the value of wireguard private IP
- Scroll down to section starting with
[wireguard] - Find line
private_ipand ensure it's set to value10.1.0.1 - The section will look like this:
[wireguard]
# Specifies whether the wireguard service is enabled on this node.
enabled = true
# Socket address this node will use for binding its wireguard interface.
# default: `0.0.0.0:51822`
bind_address = '0.0.0.0:51822'
# Private IP address of the wireguard gateway.
# default: `10.1.0.1`
private_ip = '10.1.0.1'3. Save, exit and restart the service
- If you used
nanoeditor - pressctrl+xand confirm the changes - Run these commands to update the service with new values and restart your node process:
systemctl daemon-reload && service nym-node restart-
New manual how to run
nym-nodeas non-root -
Since
v2024.13-magura, operators do not update their node version in the wallet. Manual upgrading steps has been updated accordingly. -
CLI tool
node_api_check.py, helping operators to collect all API values about their nodes locally, is not up to date with the API changes introduced withv2024.13-magurarelease version. Please treat it as unstable before we fix it.
Error Log
In case you encounter this error:
[ERROR] nym-node/src/node/mod.rs:628: the exit gateway subtask has failed with the following message: failed to start authenticator: internal wireguard error no private IP set for peer..You can follow these steps to make a workaround:
1. Find the error
-
In the node logs, locate the ERROR message which says
the exit gateway subtask has failed with the following message: failed to start authenticator: internal wireguard error no private IP set for peer KN5GPvkC+p6G/SM4PD2Z3ObAtRGiDjHPRnQOPpbdUQk= -
Copy the end part of that peer, later denoted as
<WG_PEER_STRING_END>(in our exampleGiDjHPRnQOPpbdUQk=) to use later in the sql commands
2. Fix the issue in sqlite3 db
Be careful when running commands within sqlite database.
- Navigate to the data directory:
cd $HOME/.nym/nym-nodes/<ID>/data- Enter the database:
sqlite3 clients.sqlite- Run these commands:
# Change with your unique <PEER_STRING_END>
select * from wireguard_peer where public_key like "%<WG_PEER_STRING_END>%"
# Make sure that only ONE line is returned and it contains the key
delete from wireguard_peer where public_key like "%<WG_PEER_STRING_END>%";- Confirm that peer has been removed by running this again:
select * from wireguard_peer where public_key like "%<WG_PEER_STRING_END>%";3. Exit and restart the service
Run .quit and:
systemctl restart nym-node.servicev2024.13-magura
Magura release represents a bigger milestone in project Smoosh development where nym-node is one binary able to perform any function in Nym Mixnet. This release is especially crucial for operators, please pay attention to the section Operators Updates & Tooling below.
- Release binaries (opens in a new tab)
- Release CHANGELOG.md (opens in a new tab)
nym-nodeversion1.1.10
nym-node
Binary Name: nym-node
Build Timestamp: 2024-11-18T17:02:50.947941194Z
Build Version: 1.1.10
Commit SHA: b49ef643df86f0c670672429812c632fbbaf6cf1
Commit Date: 2024-11-18T17:56:57.000000000+01:00
Commit Branch: HEAD
rustc Version: 1.82.0
rustc Channel: stable
cargo Profile: release-
New wallet version 1.2.15 (opens in a new tab) is out! - allowing operators to migrate to
nym-nodein Mixnet smart contract.
Features
-
Directory Sevices v2.1 (opens in a new tab): Read section Directory Services v2.1: API & Mixnet Contract Changes below with detailed explanation or the PR notes (opens in a new tab)
-
Switch over the last set of jobs to arc runners (opens in a new tab): Switch over the remaining GH jobs using 16-core runners to self-hosted arc runners. Since we can't currently use Docker on the ubuntu-20.04 runners, remove the matrix notification steps
Confirm that the deployment workflows work through manual testing
- cd-docs
- publish-sdk-npm
-
V2 performance monitoring feature flag (opens in a new tab): Feature flag to use v2 network monitor results in rewarding
-
Add
utoipafeature to nym-node (opens in a new tab):cargo build -p nym-nodewas failing, since its depending onQueryParamshavingutoipatraits derived -
Extract packet processing from mixnode-common (opens in a new tab): First step on a journey of making a strong interface around packet processing, and packet processing portability. This one only moves stuff around, so it should be safe to just blindly merge.
-
expose authenticator address along other address in node-details (opens in a new tab): Expose authenticator address along ip packet router and network requester for easier parsing
-
Feature/contract state tools (opens in a new tab): Introduced/reimplemented old tools for importing cosmwasm contract states given a kv dump file. This makes it significantly easier to plan and test complex state migrations on actual chains where we risk timing out on expensive operations.
-
Add env feature to clap and make clap parameters available as env variables (opens in a new tab)
-
Product DataFirst step in gateway usage data collection (opens in a new tab): This PR is the first step towards collecting data on gateway usage. It builds up on an old code for what was then nym-connect. It exposes unique users count and connection time histogram on themetrics/sessionsendpoint of the self-described API on entry-gateways. For the time being, data is collected by probing theActiveClientStoreevery minute and extracting data from this. Data is stored internally and exposed on the next day, i.e. UTC day $d$ exposes data from day $d-1$. Thestatistics(opens in a new tab) module will evolve as we add collection for product data and censorship resistance study. The collection will also eventually switch from probing to event-based for more accurate data. -
importer-clito correctly handle mixnet/vesting import (opens in a new tab) -
Import
nym-vpn-apicrates (opens in a new tab): Keep these crates in a separate workspace for now. The idea is to add them to the main workspace in time, but this appears to might require some changes to how sqlite is used. Alternatively these issues might go away once we upgrade sqlite in the main workspace. Also we intend to rename some of these to something likenym-credential-facade, and the wasm lib should be incorporated in one of the existing crates incommon. -
Product DataAdd session type based on ecash ticket received (opens in a new tab): Fire anEcashTicketevent for theGatewayStatisticsCollector, when an Ecash ticket is being accepted. This allows to mark an active session as being a mixnet session or a vpn session. It also changes the format of the related self-described data, to accommodate that new session type. -
feature: require reporting using nym-node binary for rewarded set selection (opens in a new tab)
-
Re-enable vested delegation migration (opens in a new tab): supersedes #4956 (opens in a new tab) by removing the contract migration code as it's already been run on mainnet.
-
Resolve beta clippy issues in contracts (opens in a new tab)
-
Enable global ecash routes even if api is not a signer (opens in a new tab)
-
Rename
nym-vpn-apitonym-credential-proxy(opens in a new tab) -
Make accepting t&c a hard requirement for rewarded set selection (opens in a new tab)
-
chore: update itertools in compact ecash (opens in a new tab): supersedes #4916 (opens in a new tab)
-
Adjusted ticket sizes to the agreed amounts (opens in a new tab)
-
Added
get_all_described_nodesto NymApiClient and adjusted return (opens in a new tab) -
feature: use axum_client_ip for attempting to extract source ip (opens in a new tab): improves source ip logging by extracting relevant header when nym-api is run behind a proxy
-
Added hacky routes to return nymnodes alongside legacy nodes (opens in a new tab)
-
Use unstable explorer client (opens in a new tab): Clean up stale testruns & better logging:
- use new
/unstableendpoints on explorer for backwards compatibility - log gw identity key
- better agent testrun logging
- log responses on server side
- change response code for agents
- update sqlx data
- fix agent - probe gw bug
- use new
-
chore: deprecated old nym-api client methods and replaced them when possible (opens in a new tab): this is to that the next time those methods are used outside the monorepo, the relevant calls flag up the CI via clippy
-
Fix gateway decreasing bandwidth (opens in a new tab): Make sure to update the storage after each decrease with the new values. Also set the storage values to 0 on restart for existing peers, as kernel peers can't have those values set to 0
-
Add more translations from v2 to v3 authenticator (opens in a new tab)
-
Graceful agent 1.1.5 (opens in a new tab): API improvements:
- agent exits gracefully when no testrun available
- agent reads content of server's error message in case of 503
- API doesn't log every error (to avoid log spam)
- update network probe within NS agent image: CI rebuild (opens in a new tab) of NS agent will pick up updated network probe
-
Feature/force refresh node (opens in a new tab): currently if nodes update their role from say mixnode to entry-gateway, it might take quite a while for
nym-apito pick up the change and thus they might be losing performance. With this change, the node will be force refreshed on its startup -
nym-credential-proxy-requests: reqwest use rustls-tls (opens in a new tab) -
change: dont select mixnodes bonded with vested tokens into the rewarded set (opens in a new tab)
-
Respond to auth messages with same version (opens in a new tab)
Bugfix
-
Fix critical issues SI84 and SI85 from Cure53 (opens in a new tab): This pull request fixes the following issues:
- NYM-01-009 WP5: BLS12-381 EC signature bypasses in Coconut library (Critical)
- NYM-01-014 WP5: Partial signature bypass in offline eCash (Critical)
-
bugfix: correctly paginate through 'search_tx' endpoint (opens in a new tab): when
results.append(&mut res.txs);was called,res.txswas always empty thus it was impossible to return more than page size number of results -
Bugfix/rewarder post pruning adjustments (opens in a new tab): this PR introduces/fixes the following:
- dedicated commands to request specific blocks for processing
- decreased websocket failure timeout
- ensuring we do actually have sufficient number of blocks to process rewarding for given epoch
- additional error logging
-
bugfix: fix expected return type on /v1/gateways endpoint (opens in a new tab)
-
Bugfix/additional directory fixes (opens in a new tab): This branch introduces additional fixes to the new directory services
-
Fix critical issues SI86 and SI87 from Cure53 (opens in a new tab): This pull request fixes the following issues:
- Faulty aggregation to invalid offline eCash signatures
- Signature forgery of Pointcheval-Sanders schema
-
bugfix: client memory leak (opens in a new tab): This fixes memory leaks in all the clients. however, they were most prominent in
nym-apiduring network monitoring due to the sheer amount of packets being pushed -
bugfix: directory v2.1
get_all_avg_gateway_reliability_in_intervalquery (opens in a new tab): fixes query for avg gateway performance (no idea why it makes a difference, but it does...) -
bugfix: missing #[serde(default)] for announce port (opens in a new tab)
-
bugfix: verifying signed information of legacy nodes (opens in a new tab)
-
bugfix: fixed backwards incompatibility for /gateways/described endpoint (opens in a new tab)
-
bugfix: make sure to use correct highest node id when assigning role (opens in a new tab)
-
bugfix: use old name for 'epoch_role' in SkimmedNode (opens in a new tab)
-
bugfix: use human readable roles for annotations (opens in a new tab)
-
bugfix: make gateways insert themselves into [local] topology (opens in a new tab)
-
bugfix: use bonded nym-nodes for determining initial network monitor … (opens in a new tab)
-
bugfix: make sure nym-nodes are also tested by network monitor (opens in a new tab)
-
bugfix: don't assign exit gateways to standby set (opens in a new tab)
-
bugfix: restore default http port for nym-api (opens in a new tab): when it was run under 'rocket' server the port used was 8000. let's restore that value
-
bugfix: supersede 'cb13be27f8f61d9ae74d924e85d2e6787895eb14' by using… (opens in a new tab)
-
bugfix: adjust runtime storage migration (opens in a new tab): remove the panic during migration as the gateway count can actually be different if some of them have already migrated to nym-nodes before the code has been run
-
bugfix/feature: added NymApiClient method to get all skimmed nodes (opens in a new tab)
-
bugfix: use corrext axum extractors for ecash route arguments (opens in a new tab)
-
bugfix: additional checks inside credential proxy (opens in a new tab)
-
bugfix: [wallet] displaying delegations for native nymnodes (opens in a new tab)
-
bugfix: preserve as much as possible of the rewarded set during migration (opens in a new tab)
-
bugifx: assign 'node_id' when converting from 'GatewayDetails' to 'TestNode' (opens in a new tab)
Operators Updates & Tooling
Every operator has to make sure that their nodes self-described endpoint works, otherwise the node will be un-routable and thus won't get any rewards!
-
New technical documentation: All Nym documentation starts from a new entry page nymtech.net/docs (opens in a new tab). To run locally or propose collaboration, start in our repository (opens in a new tab)
-
New Tokenomics chapter with Mixnet Rewards page
-
Nym Harbourmaster (opens in a new tab) had a new tab
NODE SEARCHwhere operators can easily search nodes by identity keys and owner accounts and get all public information listed. -
Simplified bonding and Mixnet smart contract migration
-
Nodes bonded with vesting tokens are not allowed to join rewarded set (opens in a new tab) - read more on Nym operators forum (opens in a new tab)
Wallet changes
New wallet version 1.2.15 (opens in a new tab) is out!
-
This version of wallet allows and prompts operators to migrate their gateway or mixnode to a
nym-nodein the Mixnet smart contract - an important step in project smoosh. To do so follow these steps:
1. Download the wallet from the release page (opens in a new tab)
2. Verify the binary and extract it if needed
- Download
hashes.json(opens in a new tab) - Open it with your text editor or print it's content with
cat hashes.json - Run
sha256sum <WALLET_BINARY>for examplesha256sum ./nym-wallet_1.2.15_amd64.AppImage - If your have to extract it (like
.tar.gz) do it
3. Open the wallet and sign in
4. Migrate!
- Go to Bonding and you will be prompted with such message:
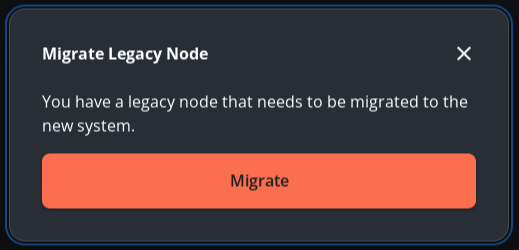
- In case you for some reason didn't see the prompt or you closed it - you can click in the upper right corner of the same window on this button:

- Confirm the transaction
5. Welcome to new episode of nym-node!
- Older versions will not allow bonding new nodes!
Selection & Rewarding
- Config score is introduced: In the current version the nodes selection to the active set has a new parameter (which multiplies the existing formula) -
config_score. Config score looks if the node binary isnym-node(not legacynym-mixnodeornym-gateway) AND if Terms & Conditions are accepted. Config score has binary values of either 0 or 1, with a following logic:
Run nym-node binary | T&C's accepted | config_score |
|---|---|---|
| True | False | 0 |
| False | True | 0 |
| False | False | 0 |
| True | True | 1 |
- The active set selection formula is then:
CONFIG_SCORE * STAKE_SATURATION * PERFORMANCE ^ 20
- Currently in Native rewarding, the rewards are split equally across the rewarded set of nodes (opens in a new tab) (which now = active set and it's size is 240 nodes) for both Mixnet mode and dVPN mode. Every node being assigned 1 / 240 work factor (hence naive rewarding).
Directory Services v2.1: API & Mixnet Contract Changes
Magura release brings breaking changes on API (opens in a new tab) logic of Nym. New APIs will only communicate with nym-node from this release and newer. Also old version of APIs won't be able to communicate with the new version of nym-node. We are also moving towards completely removing Nym Explorer API, which now has been only used to report nodes location.
Any new bonded node will provide only the bare minimum information: host, identity key and optionally custom port of its HTTP api - we highly recommend to set that one up to 8080. Everything else will be discovered via the self-described API for maximum flexibility. This also includes the sphinx key, meaning if the API is not exposed, the node will be unable to route any traffic. Furthermore, this allows to arbitrary change of nym-node from mixnode into a gateway modes (and vice versa) without losing any delegations.
The contract changes also mean any node functionality can get rewards. Rather than just with assigned mixing roles, gateways now also added into the pool. However, to be eligible for gateway rewarding, one must migrate into a nym-node on a smart contract level (or bond a new node).
API High Level Changes
New/Added
- All new routes that return multiple nodes/entries/etc now wrap their responses to expect pagination. Currently, however, full data is returned for each of the endpoints since the pagination hasn't been implemented yet. But once we add it, it won't be a breaking API change.
Removed
rocketsupport has been completely removed. All routes are now always served viaaxum
Changed
- Getting anything to do with all nodes (including gateways) requires knowing their
node_id. For legacy gateway endpoints, we have a helper method that translates identity key to thenode_id - Rewarded set is no longer populated with just mixnodes. Instead
nym-nodes are assigned to eligible roles (based on stake and performance) in the following order:- entry gateways
- exit gateways
- mixnodes
- standby
- A lot of legacy routes got deprecated. while technically they still "work" and return data, they only return data for legacy
nym-mixnodeandnym-gateway. What it means is that as operators are migrating their nodes (in the smart contract), those endpoints will start running dry. - Since layers are only assigned during rewarded set assignment, for the purposes of network monitor (v1) and legacy mixnode routes, layerless nodes are put on random layers during annotation
- All legacy gateway queries now also include additional field in their respones:
node_idthat indicate the id pre-assigned during contract migration - Nym Node performance is a bit odd. When network monitors (v1 and v2) were made, there was no concept of a Nym Node. The solution taken is checking whther there is any mixnode performance for node with a given id, if so - return it. Otherwise we grab the equivalent gateway performance. In the future it should probably be averaged or maybe split into explicit mixing or gateway routing performance metrics.
nym-api Changes
- Root route
/now redirects to/swagger
nym-node Routes
/v1/nym-nodes/annotation/<NODE_ID>- get annotation about particularnym-node, as gathered by thisnym-api. Currently this just includes last 24h performance metric and the current node role/v1/nym-nodes/bonded- get bond information about Nym Nodes, as present in the mixnet contract/v1/nym-nodes/described- get described information about Nym Nodes, as present on their self-described API/v1/nym-nodes/historical-performance/<NODE_ID>- return historical performance of thisnym-nodeon the provided date/v1/nym-nodes/performance-history/<NODE_ID>- return performance history of thisnym-node(as a 0 - 1 float)/v1/nym-nodes/uptime-history/<NODE_ID>- return current uptime of thisnym-node(as a 0 - 100 u8); added for compatibility with existing APIs using that data format/v1/nym-nodes/performance/<NODE_ID>- return current performance of thisnym-node
/v1/unstable/nym-nodes/noise- returns basic information needed for the noise protocol between nodes/v1/unstable/nym-nodes/skimmed/active- returns all: Nym Nodes and legacy mixnodes and legacy gateways, that are currently in the active set, unlessno-legacyparameter is used/v1/unstable/nym-nodes/skimmed/mixnodes/active- returns all: Nym Nodes and legacy mixnodes, that are currently in the active set, unlessno-legacyparameter is used/v1/unstable/nym-nodes/skimmed/mixnodes/all- returns all: Nym Nodes and legacy mixnodes, that are currently bonded and support mixing role, unlessno-legacyparameter is used/v1/unstable/nym-nodes/skimmed/entry-gateways/active- returns all: Nym Nodes and legacy gateways, that are currently in the active set and are assigned the entry role, unlessno-legacyparameter is used/v1/unstable/nym-nodes/skimmed/exit-gateways/active- returns all: Nym Nodes and legacy gateways, that are currently in the active set and are assigned the exit role, unlessno-legacyparameter is used/v1/unstable/nym-nodes/skimmed/entry-gateways/all- returns all: Nym Nodes and legacy gateways, that are currently bonded and support entry gateway role, unlessno-legacyparameter is used/v1/unstable/nym-nodes/skimmed/exit-gateways/all- returns all: Nym Nodes and legacy gateways, that are currently bonded and support exit gateway role, unlessno-legacyparameter is used
Deprecated (will be removed eventually, so please migrate away from their usage)
Some endpoints got purposely deprecated without any equivalent reimplemented since they do not belong on nym-api. This includes for example /stake-saturation (which can be obtained directly from the contract instead) or /inclusion-probability (for this run your own Monte Carlo simulation).
-
contract-cacheroutes - all of the below got deprecated as they will only return legacynym-mixnodeandnym-gatewaydata:/v1/gateways/v1/gateways/blacklisted/v1/mixnodes/v1/mixnodes/active- just to restate the obvious, it will only return a small SUBSET of the active set that since it will ignore active Nym Nodes/v1/mixnodes/active/detailed/v1/mixnodes/blacklisted/v1/mixnodes/detailed/v1/mixnodes/rewarded/v1/mixnodes/rewarded/detailed
-
statusroutes - all of the below got deprecated as they will only return legacynym-mixnodeandnym-gatewaydata:/v1/status/gateway/<ID_KEY>/report/v1/status/gateway/<ID_KEY>/history/v1/status/gateway/<ID_KEY>/core-status-count/v1/status/gateway/<ID_KEY>/avg_uptime/v1/status/gateways/detailed/v1/status/gateways/detailed-unfiltered/v1/status/mixnode/<MIX_ID>/report/v1/status/mixnode/<MIX_ID>/history/v1/status/mixnode/<MIX_ID>/core-status-count/v1/status/mixnode/<MIX_ID>/avg_uptime/v1/status/mixnodes/detailed/v1/status/mixnodes/detailed-unfiltered/v1/status/mixnode/<MIX_ID>/status/v1/status/mixnode/<MIX_ID>/reward-estimation/v1/status/mixnode/<MIX_ID>/compute-reward-estimation/v1/status/mixnode/<MIX_ID>/stake-saturation/v1/status/mixnode/<MIX_ID>/inclusion-probability/v1/status/mixnodes/inclusion_probability/v1/status/mixnodes/rewarded/detailed/v1/status/mixnodes/active/detailed
-
nym-noderoutes - all of the below got deprecated as they will only return legacynym-mixnodeandnym-gatewaydata:/v1/gateways/described/v1/mixnodes/described
-
Unstable Nym Nodes Routes:/v1/unstable/nym-nodes/mixnodes/skimmed- due to inconsistency in behaviour (i.e. active vs all) it is now redirected to/v1/unstable/nym-nodes/mixnodes/skimmed/activeand unwraps the pagination/v1/unstable/nym-nodes/gateways/skimmed- due to inconsistency in behaviour (i.e. active vs all) it is now redirected to/v1/unstable/nym-nodes/entry-gateways/skimmed/alland unwraps the pagination
Unstable Nym Nodes Routes:/v1/unstable/nym-nodes/skimmed- now works withexitparameter/v1/unstable/nym-nodes/skimmed- introducedno-legacyflag to ignore legacynym-mixnodeandnym-gateway(where applicable)/v1/unstable/nym-nodes/skimmed- will now return all nodes if no query parameter is provided
Mixnet Contract
Every operator has to make sure that their nodes self-described endpoint works, otherwise the node will be un-routable and thus won't get any rewards!
High Level Changes
New/Added
- All new nodes are now bonded as Nym Nodes, even when using old
BondMixnodeorBondGatewaymessages (messages are getting translated) - Operators only announce nodes identity key (
<ID_KEY>), host and port to the directory. Everything else is discovered via self-described endpoint - All Nym Nodes in the rewarded set are eligible for rewards and staking. Even if they serve one of the gateway roles. Legacy gateways can't be staked on nor get rewards.
- All nodes, including legacy mixnodes and legacy gateways, are now uniquely identified by a monotonically increasing
node_id - All legacy gateways are preassigned
node_idduring the contract migration
Removed
🔥 all concepts of node families got purged, removed, deleted, thrown into the abyss. they simply no longer exist and the world is all better for it.
Changed
- Bunch of types got changed/renamed with some fields being added/removed/deprecated. It's be quite a lot of work to list them all here, but whenever possible and feasible, they should be cross-compatible (but not always).
- Rewarded set is no longer just a "number". Instead it has an explicit number of all
nym-nodemodes: mixnodes, entry and exit gateways as well as standby nodes - Rewarding is now based on two parameters: performance and work factor as opposed to performance and "is active" flag. However, in practice, during this transitional period, it is assumed that the work factor will be equivalent to what would have been calculated using the old "is active" flag
Transaction Messages Changes
BondNymNode- self-explanatoryUnbondNymNode- self-explanatoryUpdateNodeConfig- works asUpdateMixnodeConfig; it lets you change your announced host or http api portMigrateMixnode- migrate your existing legacy mixnode into a Nym NodeMigrateGateway- migrate your exsting legacy gasteway into a Nym Node. enables staking and rewardingAssignRoles- an additional step for epoch transition transactions. think of it as a replacement forAdvanceCurrentEpoch. it assigns nodes to particular roles for the given epoch
- As mentioned, all family-related things got killed off, so the following no longer exist:
CreateFamily,JoinFamily,LeaveFamily,KickFamilyMember,CreateFamilyOnBehalf,JoinFamilyOnBehalf,LeaveFamilyOnBehalf,KickFamilyMemberOnBehalf UpdateActiveSetSize- the rewarded/active set are now based on the role distributionAssignNodeLayer- we're no longer explicitly assigning roles to all mixnodes, instead they get assigned mixing rolesAdvanceCurrentEpoch- the logic for advancing the epoch/assigning active set has changed so this message was removed
v2024.12.1-aero - patch
- Release binaries (opens in a new tab)
nym-nodepatch only, no other binaries
nym-node
Binary Name: nym-node
Build Timestamp: 2024-11-07T08:45:13.162565620Z
Build Version: 1.1.9-1
Commit SHA: ccdee808303ffcfa8ed77176d3f629512045febb
Commit Date: 2024-11-06T16:31:30.000000000+01:00
Commit Branch: HEAD
rustc Version: 1.82.0
rustc Channel: stable
cargo Profile: releaseChanges
- Fixed timeout connectivity issues with authenticator
- Amended network allowance cap
v2024.12-aero
- Release binaries (opens in a new tab)
- Release CHANGELOG.md (opens in a new tab)
nym-nodeversion1.1.9
nym-node
Binary Name: nym-node
Build Timestamp: 2024-10-17T08:57:52.525093253Z
Build Version: 1.1.9
Commit SHA: d75c7eaaaf3bb7350720cf9c7657ce3f7ee6ec2e
Commit Date: 2024-10-17T08:51:39.000000000+02:00
Commit Branch: HEAD
rustc Version: 1.81.0
rustc Channel: stable
cargo Profile: releaseFeatures
-
Rust sdk stream abstraction (opens in a new tab): Starting to move this from being standalone binaries (as seen here (opens in a new tab)) into the sdk. EDIT this has sort of expanded a bit to include a few things:
- simple example
- example doc to
src/tcp_proxy.rs - simple echo server in
tools/ - multithread example
- example to sdk for using different network
- go ffi for proxies
-
Build(deps): bump
tomlfrom0.5.11to0.8.14(opens in a new tab):toml(opens in a new tab) version update
- Ensured that the
cargo.tomlis legible in various places; tested it onnym-node,nym-apiandnymvisor. - Ensured that updating the cargo.toml file and restarting the given binary continues to behave as normal.
-
Use
serdefrom workspace (opens in a new tab): cargo autoinherit forserde- cargo autoinherit forbs58andvergenincosmwasm-smart-contracts -
Gateway database modifications for different modes (opens in a new tab): As gateway clients will not be solely from the mixnet, we need to split the table that handles shared keys from the client ids that are referenced from other tables. That way, the bandwidth table can be shared between different client types (entry mixnet, entry gateway, exit gateway), using the same
client_idreferencing. -
Remove the push trigger for
ci-nym-wallet-rust(opens in a new tab) -
Chore: remove queued migration for adding explicit admin (opens in a new tab)
-
Allow clients to send stateless gateway requests without prior registration (opens in a new tab): in order to make changes to the registration/authentication procedure we needed a way of extracting protocol information before undergoing the handshake.
-
Feature/updated gateway registration (opens in a new tab): This PR introduces support for aes256-gcm-siv shared keys between clients and gateways.
- Those changes should be fully backwards compatible. if they're not, there's a bug.
- For the following combinations I inited the client, ran the client, stopped the client, and ran the client again:
- Fresh client on new binary && gateway on old binary
- Fresh client on old binary && gateway on new binary
- Fresh client on new binary && gateway new binary
- Existing old client on old binary & new gateway
-
Entry wireguard tickets (opens in a new tab): Note: The behaviour of the nodes and vpn client (as a test) has not changed, it still works as it used to. Obtaining ticketbooks also is unchanged
-
Update
nym-vpnmetapackage and replacenymvpn-xwithnym-vpn-app(opens in a new tab): Change dependency fromnymvpn-xtonym-vpn-appto reflect the new package name of the tauri client -
Remove clippy github PR annotations (opens in a new tab): It eats up CI resources and time to run the clippy annotation checks that likely no one uses anyway. We keep the clippy checks of course.
-
Update cargo deny (opens in a new tab): Update to use latest
cargo-deny. Here are the steps done:- Regenerate
deny.toml - Backport old settings to
deny.toml - Explicitly allow GPL-3 only on our own specific crates
- Update
deny.tomlfor latest changes - Fix
cargo-denywarnings for duplicate crates - Update
cargo-deny-actionto v2
- Regenerate
-
Data Observatory stub (opens in a new tab): You need Postgres up for
sqlxcompile-time checked queries to work
./pg_up.sh- Play with the database:
docker exec -it nym-data-observatory-pg /bin/bash
psql -U youruser -d yourdb-
Proxy ffi (opens in a new tab): Updates Go & CPP FFI with the proxy code from #4743 (opens in a new tab)
-
Bump
http-api-clientdefault timeout to 30 sec (opens in a new tab) -
Check both version and type in message header (opens in a new tab)
-
nym-node: don't use bloomfilters for double spending checks (opens in a new tab): this PR disables gateways polling for double spending bloomfilters and alsonym-apisfrom providing this data.
Bugfix
-
Fix
apt installinci-build-upload-binaries.yml(opens in a new tab) -
Fix missing duplication of modified tables (opens in a new tab)
-
Fix nymvpn.com url in mainnet defaults (opens in a new tab): The old URL (nympvn.net) works since it is redirected to nymvpn.com, but the extra round-trip adds latency to all the API calls the vpn client does. So this PR should help speed things up, in particular when these API calls happen across the mixnet.
-
Replace unreachable macro with an error return (opens in a new tab)
Operators Guide, Tooling & Updates
Documentation Updates
- Update FAQ sphinx size (opens in a new tab): This PR upgrades url to our code base sphinx creation from an outdated branch to develop.
Fast & Furious - WireGuard edition
Nym team started another round of load and speed testing. This time the tests are limited to Wireguard mode Gateways - to find out any weak spots for needed improvement. The load testing is happening directly on mainnet as it simulates a real user traffic which the network components must be able to handle in order.
Over past week we ran a total of three tests, with 450 clients at most. We've managed to push around 300 GB in total. Around 50% of requests failed. Over the course of those three tests, we did about 5000 requests, and bandwidth per client varies between 50Mb/s and 150Mb/s.
We already caught two bugs and fixed (opens in a new tab) it in this release.
The faster the operators upgrade to this latest release (opens in a new tab), the better. A that will allow us to do more precise testing through the nodes without the registry bug, leading to more precise specs for nym-node.
Here are the aims of these tests:
- Understanding of the wireguard network behavior under full load
- How many client users can all entry gateways and exit gateways handle simultaneously?
- How much sustained IP traffic can a subset of mainnet nodes sustain?
- Needed improvements of Nym Node binaries to improve the throughput on mainnet
- Measurement of required machine specs
- Releasing a new spec requirements
- Raw data record
- Increase quality of Nym Nodes
Meanwhile we started to research pricing of stronger servers with unlimited bandwidth and higher (and stable) port speed, to arrive to a better understanding of needed rewards and grants to bootstrap the network before NymVPN launch.
More info about testing and tools for performance monitoring can be found in this chapter.
We would like to call out to operators to join the efforts and reach out to us if they know of solid ISPs who offer reliable dedicated services for good price or may even be interested in partnership.
Delegation Program
In October we again proceeded with our Delegation Program. 22 nodes didn't meet the program rules and got their delegation removed and 25 nodes from the que received delegation. Below is a complete list.
Delegated:
Ce6kcPckNfQsga2z645VFQYadtoTjqXrS1YXMTtNNv98
2XSCWy1vAoJRaYBJXx4KWwjU1cfoS2wNBXVQZvi8Jtdr
Bu4sUGjJqkje4vSncTH2KgrnojmfESdaYwamC6DbpJGZ
7TWEw9qQxsc8w4WhPAX6zjZ8vuNBdtP21zUVN8K26RkD
HejyqervmGTCEwi1JbRBXV5My463336huBn8ZgSpuhc3
CXcCVGiamYSwgVwaxW3mEkXkZh1sKY2TXnWjjTjxDxzA
FScLfnKUPv9wSef3R4N2pQ9ft7DiwdivLW1i65Dqfc9L
2vuZZJjyYN27fvDbhyqeGosewGWaRh6iVsFtqbJoYAR7
B9QiBsSAx7MRcTpYMs1fu9AFJurAZTPWMispHZXPbaVW
E3e2a9kXZjQXsKAfvmCf2WqwmVkiGR2LbjCwoadZgEJt
Dk4fCLM7idHPqfsUucLQtSMtYaYCLhi4T7vwvw88jG3P
9xZUp4sYWUNJesWy3MPVjh5kTorNqj3RxcFgBmYjV1xV
HK9QxPpdJfNtNpLJZHTN5M113jeBbFzTkMtPt9eouimx
ECkzyHfoiNGKyDTtbbH5HDCWa8KMGh92mtGbGHLZ3Y9n
9jQQV9vQ2mFFXywwVhACCKefjUFpyBoCU6KXNfjAEi45
6QguhCfnDPKJe8bQXg9myuPB89yYFk6R77vMhLTbipK7
4hAJJQhLTFve8FZGd28ksjavbch8STMax2rytzKmDPCV
EZLFq5HGXFKRpxu78nVjf7kuuUaKPLAbezR6mXbZrP6y
FtAAA5GMxY1Ge9wKYDrQgaSfJEUp4XvBLptBwy3GU8ap
tUiLPjz5nkPn5ZJT5ZXLPGDcZ3caQsfkMAp1epoAuSQ
4ScsM6AVowhKTMWaH98NLntKDwbu2ZMEycUk4mZiZppG
Hb34PTth6CeFziPAAEUMEjJFHWJg1dDex5QxUXKNqRBE
9ek1PMvLhpbwZe7kTMyCVY5VNqrdSPPoruFPQtbxnZyfUndelegated due to the use of an outdated binary:
9UHXFYuMLhuugndt8xCFRydmDPFyEEUHYc72tNANEtHp
5Y86A7fUX3LYVDDeoujtAiZFudYcHJq6gw8nsp71wN7U
HYWjn6yL8y7TBPFL9bTgDm6tHgyoEQupgJuBhLLoA5EY
4JCpbdhiQFKWwhrbkNDbwcwBGZnvU4WQrF2vqQLfmZvW
2f7JaYmmrMQQMczLX32ogfP7PBHeyPKbAVNjjEsExZVd
9TW55JrsFhsMoe3Tf8LBR4bPSCX86VXyvioMmCw9tWB
AyN34XqUi5XxgjmivWG2z6TftkqAFjVV5C9zCbx8Fvp5
skNS4zNsKdbbUR9wFTJoPdmReW4NdrDEpp8512TNG4f
DztUnMKM545sdipgqhCsPNhK3YVmBbS2fp9HZgM5Jpw9
GnLmx1s7g9nH3uLRhGpaXTbQEhCSKB6YenBQWQhthSx9
GoJjAkH5hpcPYeW7JDUVfHdqgcufjwdhY2PLwBGJV3Ar
EdHVMTXpLiBbvCUnEoSPQ86pBNY1h9HtL34Q7cpNPWCyUndelegated due to increased operation costs or profit margin:
Erw9AQ4UJCgCiAWisUWbFk9Yedm8qvW4YQqmJRrBrE5p
BVDVtmNbZRgPKU81uBkrgfj5TnhtZqQcPAwxD48jcfMd
36nmH3kawhAsNA6sxFva2HgTnQHQDbcrRefvWWbmhHvY
2831fyXRAJ88x1Pd5aW7utw7WH1XkHZEfoWhLk2foLxJ
AMDS4cib433iRstwP9mWnZ4zPqb6hm6uPF7PpvhSkpYC
DE9eEeVsuiKeVfwebg5HYsebqRUvxd7LWsT9hQUtVrTQ
FAKhiQ8nW5sAWAxks1WB8u1MAWsapToCSE3KmF9LuGRQUndelegated due to being blacklisted for extensive period
sjL9n9ymxfWWwkQJxXdsMkdwamXfh3AJ3vCe7rJ8RrT
E2HAJrHnk56QZDUCkcjc4i4pVEqtyuPYL5bNFYtweQuL
4PytR3tmodsvqGTKdY47yie8kmrkARQdb5Ht3Ro3ChH4v2024.11-wedel
- Release binaries (opens in a new tab)
- Release CHANGELOG.md (opens in a new tab)
nym-nodeversion1.1.8
Binary Name: nym-node
Build Timestamp: 2024-09-27T11:02:37.073944654Z
Build Version: 1.1.8
Commit SHA: c3ec970a377adb25d57be5428551fada2ec55128
Commit Date: 2024-09-26T08:24:53.000000000+02:00
Commit Branch: master
rustc Version: 1.80.1
rustc Channel: stable
cargo Profile: releaseFeatures
-
New Network Monitor (opens in a new tab): Monitors the Nym network by sending itself packages across the mixnet. Network monitor is running two tokio tasks, one manages mixnet clients and another manages monitoring itself. Monitor is designed to be driven externally, via an
HTTP api. This means that it does not do any monitoring unless driven by something likelocust(opens in a new tab). This allows us to tailor the load externally, potentially distributing it across multiple monitors. Includes a dockerised setup for automatically spinning up monitor and driving it with locust.- Note: NNM is not deployed on mainnet yet!
-
Add get_mixnodes_described to validator_client (opens in a new tab)
-
Remove deprecated mark_as_success and use new disarm (opens in a new tab): Update function name to keep terminology consistent with tokio
CancellationToken DropGuard. -
Update peer refresh value (opens in a new tab):
lsoexpose the value by moving it to wireguard types, and separate the refresh time to the database sync time, so that more probable and needed actions happen faster (refresh) and more improbable ones don't overload the system (peer suspended or stale)
- Noted that the constants
DEFAULT_PEER_TIMEOUTandDEFAULT_PEER_TIMEOUT_CHECKhave been moved tocommon/wireguard-types/src/lib.rsand are now being used across modules for consistency - Observed that the
peer_controller.rsnow separates the in-memory updates from the storage sync operations to reduce system load - Identified that in-memory updates of peer bandwidth usage happen every
DEFAULT_PEER_TIMEOUT_CHECK(every 5 seconds), while storage updates occur every 5 *DEFAULT_PEER_TIMEOUT_CHECK(every 25 seconds)
Checked System Load and Performance:
-
Monitored system resource usage (CPU, memory, I/O) during the test to assess the impact of the changes
-
Confirmed that the separation of in-memory updates and storage syncs resulted in reduced system load, particularly I/O operations, compared to previous versions where storage updates occurred more frequently
-
Ensured that the system remained responsive and no performance bottlenecks were introduced
-
Efficiency Improvement: The separation of in-memory updates and storage syncs effectively reduced unnecessary database writes, improving system efficiency without compromising data accuracy
-
Remove duplicate stat count for retransmissions (opens in a new tab)
-
Make gateway latency check generic (opens in a new tab): Replace concrete gateway type with trait in latency check, so we can make use of it in the vpn client.
- Initialised new
nym-clientwith the--latency-based-selectionflag and ensured it still works as normal.
-
Avoid race on ip and registration structures (opens in a new tab): To avoid a state where the ip is being cleared out before the registration is also cleared out, couple the two structures under the same lock, since they are anyway very inter-dependent.
-
- Checked out the release/2024.10-wedel branch containing the fix for the race condition on IP and registration structures
- Deployed the on a controlled test environment to prevent interference
-
Monitored Logs:
- Enabled debug logging to capture all events
- Monitored logs in real-time to observe the handling of concurrent registration requests
- Checked for any error messages, warnings, or indications of race conditions
-
Verified Client Responses:
- Ensured that all clients received appropriate responses:
- Successful registration with assigned IP and registration data
- Appropriate error messages if no IPs were available or if other issues occurred
- Confirmed that no clients were left in an inconsistent state (e.g., assigned an IP but not fully registered)
-
Validated Normal Operation:
- Conducted standard registration processes with individual clients to confirm that regular functionality is unaffected via
nym-vpn-cli - Ensured that authenticated clients could communicate over the network as expected
- Conducted standard registration processes with individual clients to confirm that regular functionality is unaffected via
-
Enable dependabot version upgrades for root rust workspace (opens in a new tab)
-
Fix clippy for
unwrap_or_default(opens in a new tab): Fix nightly build for beta toolchain (opens in a new tab) -
Update dependabot (opens in a new tab): Bump max number of dependabot rust PRs to 10. Add readme entry to workspace package.
-
Run
cargo-autoinheritfor a few new crates (opens in a new tab): Run cargo-autoinherit for a few new crates - Sort crates list. -
Add
axumserver tonym-api(opens in a new tab): Summary PR to add axum functionality behind a feature flagaxum, alongside rocket. -
Expose wireguard details on self described endpoint (opens in a new tab)
Wireguard details are now visible at the nym-node endpoint /api/v1/gateway/client-interfaces as well as on the nym-api self-described endpoint /api/v1/gateways/described, above the existing data displaying mixnet_websocket information.
An example of what will be shown is:
"wireguard": {
"port": 51822,
"public_key": "<some public key here>"
}- Revamped ticketbook serialisation and exposed additional cli methods (opens in a new tab):
wipbranch that includes changes needed forvpn-apialongside additionalecash utils
Checked the following commands:
show-ticket-books # which displays the information about all ticketbooks associated to the client
import-ticket-book # which imports a normal ticketbook to the client alongside `--full` flagOn the cli, the following were added: import-coin-index-signatures, import-expiration-date-signatures and import-master-verification-key.
-
Run cargo autoinherit following last weeks dependabot updates (opens in a new tab)
-
Create nym-repo-setup debian package and nym-vpn meta package (opens in a new tab): Create nym-repo-setup debian package that sets up the nymtech debian repo on the system it's installed on. It does 2 things:
- Copy the keyring to
/usr/share/keyrings/nymtech.gpg - Copy the repo spec to
/etc/apt/sources.list.d/nymtech.list
- Also create a meta package
nym-vpnwhich only purpose is to depend on the daemon and UI.
- Copy the keyring to
- Install with
sudo dpkg -i ./nym-repo-setup.deb- Once it's installed, it should be possible to install the vpn client with
sudo apt install nym-vpnc- To remove the repo, use
sudo apt remove nym-repo-setupNOTE: removing the repo will not remove any installed nym-vpn packages
-
Downloaded the
nym-repo-setup.debpackage to a Debian-based test system -
Installed the repository setup package using the command:
sudo dpkg -i ./nym-repo-setup.deb- Verified that the GPG keyring was copied to
/usr/share/keyrings/nymtech.gpg:
ls -l /usr/share/keyrings/nymtech.gpg- Checked that the repository specification was added to
/etc/apt/sources.list.d/nymtech.list:
cat /etc/apt/sources.list.d/nymtech.list- Updated the package list:
sudo apt update- Installed the VPN client meta-package:
sudo apt install nym-vpnc-
Confirmed that the
nym-vpncpackage and its dependencies (daemon and UI) were installed successfully -
Tested the VPN client to ensure it operates as expected
-
Removed the repository setup package:
sudo apt remove nym-repo-setup-
Verified that the repository specification file
/etc/apt/sources.list.d/nymtech.listwas removed -
Ensured that the installed
nym-vpncpackages remained installed and functional after removing the repo setup package
-
Use ecash credential type for bandwidth value (opens in a new tab)
-
Start switching over jobs to arc-ubuntu-20.04 (opens in a new tab)
ci-binary-config-checker - ci-build-upload-binaries
- ci-build
- ci-cargo-deny
- ci-contracts-schema
- ci-contracts-upload-binaries
- ci-contracts
- ci-docs
- ci-nym-wallet-rust
- ci-sdk-wasm-
Move credential verification into common crate (opens in a new tab)
-
Remove
golangworkaround inci-sdk-wasm(opens in a new tab) -
Disable push trigger and add missing paths in
ci-build(opens in a new tab) -
chore: removed completed queued mixnet migration (opens in a new tab)
Bugfix
-
Fix test failure in ipr request size (opens in a new tab): Nightly build started failing due to a unit test using
now(), changing the serialized size. Fixed to use a fixed date. -
Fix clippy for nym-wallet and latest rustc (opens in a new tab)
-
Allow updating globally stored signatures (opens in a new tab)
-
Bugfix/ticketbook false double spending (opens in a new tab)
Tested running a client in mixnet mode, with a standard ticketbook, as well as a client using an imported ticketbook. The double spending bug is no longer an issue, bandwidth is consumed properly, and upon consumption of one ticket another ticket is properly obtained.
Operators Guide, Tooling & Updates
-
WSS setup guide updates (opens in a new tab): Operators setting up WSS and reverse proxy on Gateways have now cleaner and simpler guide to configure their VPS.
-
Updat hostname instruction for WSS (opens in a new tab): Adding a hostname instruction for clarity
nym-node patch from release/2024.10-caramello
Binary Name: nym-node
Build Timestamp: 2024-09-16T15:00:41.019107021Z
Build Version: 1.1.7
Commit SHA: 65c8982cab0ff3a1154966e7d61956cb42a065fc
Commit Date: 2024-09-16T15:59:34.000000000+02:00
Commit Branch: HEAD
rustc Version: 1.81.0
rustc Channel: stable
cargo Profile: releaseThis patch fixes v202410-caramello release bug where one of the used dependencies - DefGuard (opens in a new tab), was failing.
Updating to this patched version and running nym-node --mode exit-gateway with --wireguard-enabled true should result in a smooth node start without the defguard_wireguard error, occuring to some operators before:
/home/ubuntu/.cargo/registry/src/index.crates.io-6f17d22bba15001f/defguard_wireguard_rs-0.4.2/src/netlink.rs:155: Serialized netlink packet (23240 bytes) larger than maximum size 12288: NetlinkMessage.This release is a patch only, there are no additional features, everything else stays the same like in the latest release v202410-caramello.
v2024.10-caramello
- Release binaries (opens in a new tab)
- Release CHANGELOG.md (opens in a new tab)
nym-nodeversion1.1.7
- Backport 4844 and 4845 (#4857 (opens in a new tab))
- Bugfix/client registration vol2 (#4856 (opens in a new tab))
- Remove wireguard feature flag and pass runtime enabled flag (#4839 (opens in a new tab))
- Eliminate cancel unsafe sig awaiting (#4834 (opens in a new tab))
- added explicit updateable admin to the mixnet contract (#4822 (opens in a new tab))
- using legacy signing payload in CLI and verifying both variants in contract (#4821 (opens in a new tab))
- adding ecash contract address (#4819 (opens in a new tab))
- Check profit margin of node before defaulting to hardcoded value (#4802 (opens in a new tab))
- Sync last_seen_bandwidth immediately (#4774 (opens in a new tab))
- Feature/additional ecash nym cli utils (#4773 (opens in a new tab))
- Better storage error logging (#4772 (opens in a new tab))
- bugfix: make sure DKG parses data out of events if logs are empty (#4764 (opens in a new tab))
- Fix clippy on rustc beta toolchain (#4746 (opens in a new tab))
- Fix clippy for beta toolchain (#4742 (opens in a new tab))
- Disable testnet-manager on non-unix (#4741 (opens in a new tab))
- Don't set NYM_VPN_API to default (#4740 (opens in a new tab))
- Update publish-nym-binaries.yml (#4739 (opens in a new tab))
- Update ci-build-upload-binaries.yml (#4738 (opens in a new tab))
- Add NYM_VPN_API to network config (#4736 (opens in a new tab))
- Re-export RecipientFormattingError in nym sdk (#4735 (opens in a new tab))
- Persist wireguard peers (#4732 (opens in a new tab))
- Fix tokio error in 1.39 (#4730 (opens in a new tab))
- Feature/vesting purge plus ranged cost params (#4716 (opens in a new tab))
- Fix (some) feature unification build failures (#4681 (opens in a new tab))
- Feature Compact Ecash : The One PR (#4623 (opens in a new tab))
Features
Scenario 1: Bandwidth Decreasing Continuously
- Started the client and noted the initial bandwidth (e.g., 1GB).
- Used the client and tracked bandwidth usage over time (e.g., decrease by 100MB every hour).
- Restarted the client after some usage.
- Verified the bandwidth continued from the last recorded value, not reset.
The bandwidth continued decreasing without resetting upon restart. Logs and reports correctly reflected the decreasing bandwidth.
Scenario 2: Bandwidth Reset Next Day
- Used the client normally until the end of the day.
- Suspended some clients and kept others active.
- Checked bandwidth at midnight.
- Verified that bandwidth reset to 1GB for both suspended and active clients.
Bandwidth reset to 1GB for all clients at midnight. Logs and reports correctly showed the reset.
Scenario 3: Bandwidth Reset at a Different Time (e.g., Midday)
- Configured the system to reset bandwidth at midday.
- Used the client and monitored bandwidth until midday.
- Kept the client connected during the reset time.
- Verified that bandwidth reset to 1GB live at midday.
Bandwidth reset to 1GB at midday while the client was connected. Logs and reports correctly reflected the reset.
Scenario 4: Stale Check for 3 Days
- Kept a client inactive for 3 days.
- Verified removal from the peer list after 3 days.
- Reconnected the client after 3 days and checked for a new private IP.
- Restarted a client within 3 days and verified it retained the same private IP.
The client was removed from the peer list after 3 days of inactivity. Upon re-connection after 3 days, the client received a new private IP. The client retained the same private IP when restarted within 3 days.
-
Feature/merge back (opens in a new tab): Merge back from the release branch the changes that fix the
nym-nodeupgrades -
Removed mixnode/gateway config migration code and disabled cli without explicit flag (opens in a new tab): Commands for archived / legacy binaries
nym-gatewayandnym-mixnodewon't do anything without explicit--force-runto bypass the deprecation. The next step, in say a month or so, is to completely remove allclirelated things.
- Verify that the
nym-gatewaybinary andnym-mixnodebinary commands return the error message stating to update to nym-node - Check that when adding the
--force-runflag, it still allows the command to be run (aside frominitwhich has been removed) and the message stating to update to nym-node is a warning now - Check
nym-nodeis not affected - Reviewed the changes in the PR
- Handle clients with different versions in IPR (opens in a new tab): Allow the IPR to handle clients connecting both using
v6andv7, independently. The motivation is that we want to be able to roll out a API version change gradually for VPN clients without breaking backwards compatibility. The main feature on the newv7format that is not yet used, is that it adds signatures for connect/disconnect.
Run the same command (using same gateways deployed from this PR) on different versions of the nym-vpn-cli.
Example:
sudo -E ./nym-vpn-cli -c ../qa.env run --entry-gateway-id $entry_gateway --exit-gateway-id $exit_gateway --enable-two-hop
sudo -E ./nym-vpn-cli -c ../qa.env run --entry-gateway-id $entry_gateway --exit-gateway-id $exit_gateway --enable-two-hop-
Remove wireguard feature flag and pass runtime enabled flag (opens in a new tab)
-
Added explicit updateable admin to the mixnet contract (opens in a new tab)
-
Using legacy signing payload in CLI and verifying both variants in contract (opens in a new tab)
-
Check profit margin of node before defaulting to hardcoded value (opens in a new tab)
-
Update publish-nym-binaries.yml (opens in a new tab): Adds wireguard to builds
-
Update ci-build-upload-binaries.yml (opens in a new tab): Adds wireguard for ci-builds
-
Re-export RecipientFormattingError in nym sdk (opens in a new tab)
-
Feature/vesting purge plus ranged cost params (opens in a new tab): Combines #4715 (opens in a new tab) and #4711 (opens in a new tab) into one.
- Disables all non-essential operations on the vesting contract => you can no longer bond mixnodes/make delegations/etc. (you can still, however, withdraw your vested tokens and so on)
- Introduces admin-controlled minimum (and maximum) profit margin and interval operating costs.
- both contracts have to be migrated at the same time. ideally within the same transaction
- mixnet contract migration is not allowed (and will fail) if there are any pending actions involving vesting tokens, like delegating, increasing pledge, etc
-
Bump braces from
3.0.2to3.0.3in/nym-wallet/webdriver(opens in a new tab): Bumps braces (opens in a new tab) from3.0.2to3.0.3.
Bugfix
- Building all binaries is ok
- Running
cargo fmtreturns no issues
Tested updating an old nym-node version and ensuring it did not throw any errors.
-
Fix tokio error in
1.39(opens in a new tab):- Bump tokio to
1.39.2, skipping the issue with1.39.1
- Bump tokio to
-
Fix (some) feature unification build failures (opens in a new tab): Running a script in the root workspace that builds each crate independently
#!/bin/bash
packages=$(cargo metadata --format-version 1 --no-deps | jq -r '.packages[].name')
# Loop through each package and build
for package in $packages; do
echo "Building $package"
cargo clean
cargo check -p "$package"
if [ $? -ne 0 ]; then
echo "Build failed for $package. Stopping."
exit 1
fi
done-
bugfix: make sure DKG parses data out of events if logs are empty (opens in a new tab): This will be the case on post
0.50chains -
Fix clippy on rustc beta toolchain (opens in a new tab): Fix clippy warnings for rust beta toolchain
-
Fix clippy for beta toolchain (opens in a new tab): Fix beta toolchain clippy by removing unused module
- Add
nym-prefix toserde-commoncrate - Remove ignored
default-features = falseattribute for workspace dependency
- Add
Crypto
Operators Guide, Tooling & Updates
-
More explicit setup for
nym-nodewith a new option explanation, including syntax examples -
Wireguard builds from source together with
nym-node, no need to specify with a feature flag anymore -
Wireguard peers stay connected for longer time, re-connections are also faster
-
Profit margin and operating cost values are set to the values agreed by operators off-chain vote, the values can be changed in the future through Nym Operators governance process (opens in a new tab)
Minimum profit margin = 20%
Maximum profit margin = 50%
Minimum operating cost = 0 NYM
Maximum operating cost = 1000 NYM
-
Nym Harbourmater (opens in a new tab) has several new functionalities:
- Version counting graph for Gateways and Mixnodes
- Several new columns with larger nodes performance and settings overview.
- Top routing score now includes:
- Wireguard registration and complete handshake test, to configure see tasklist below
- DNS resolution check, to configure see tasklist below
- Wireguard perfomance bigger than 0.75, to configure see tasklist below
-
New Nym Wallet (opens in a new tab) is out!
- Vesting contract functionalities have been purged, users can only remove tokens from vesting
- Migrating from
mixnodeorgatewaysmart contracts to a new unifyingnym-nodesmart contract will be available soon using Nym desktop wallet, just like you are used to for bonding and node settings. After this migration allnym-nodeswill be able to receive delegation and rewards. We will share a step by step guide once this migration will be deployed. No action needed now.
-
Nym API Check CLI is upgraded according to the latest API endpoints, output is cleaner and more concise.
Operators Tasks
The steps below are highly recommended for all operators and mandatory for everyone who is a part of Nym Delegation or Grant program. Deadline is Friday, September 20th, 2024.
Every nym-node should be upgraded to the latest version! Operators can test using Sandbox env during the pre-release period, then upgrade on mainnet. During the upgrade, please follow the points below before you restart the node:
nym-node
- Make sure to fill in basic description info, into the file located at
.nym/nym-nodes/<ID>/data/description.toml(all nodes) - Configure wireguard routing with new
network_tunnel_manager.sh(opens in a new tab) following these steps (Gateways only for the time being) - Enable Wireguard with
--wireguard-enabled trueflag included in your run command (Gateways only for the time being)- Note: On some VPS this setup may not be enough to get the correct results as some ISPs have their own security groups setup below the individual VPS. In that case a ticket to ISP will have to be issued to open the needed settings. We are working on a template for such ticket.
- Setup reverse proxy and WSS on
nym-node(Gateways only for the time being) - Don't forget to restart your node - or (preferably using systemd automation) reload daemon and restart the service
- Optional: Use
nym-gateway-probeand NymVPN CLI (opens in a new tab) to test your own Gateway - Optional: Run the script below to measure ping speed of your Gateway and share your results in Nym Operators channel (opens in a new tab)
We made a script for pinging nymtech.net from your GWs. Can you please install it and then share the result together with your Gateway ID:
- Get the script onto your machine (soon on github for curl or wget):
# paste all this block as one command
cat <<'EOL' > ping_with_curl_average_for_wg_check.sh
#!/bin/bash
ping_with_curl_average_for_wg_check() {
total_connect_time=0
total_total_time=0
iterations=5
timeout=2
for ((i=1; i<=iterations; i++)); do
echo "ping attempt $i..."
echo "curling nymtech.net to check ping response times"
times=$(curl -I https://nymtech.net --max-time $timeout \
-w "time_connect=%{time_connect}\ntime_total=%{time_total}" -o /dev/null -s)
time_connect=$(echo "$times" | grep "time_connect" | cut -d"=" -f2)
time_total=$(echo "$times" | grep "time_total" | cut -d"=" -f2)
total_connect_time=$(echo "$total_connect_time + $time_connect" | bc)
total_total_time=$(echo "$total_total_time + $time_total" | bc)
echo "time to connect: $time_connect s"
echo "total time: $time_total s"
done
average_connect_time=$(echo "scale=3; $total_connect_time / $iterations" | bc)
average_total_time=$(echo "scale=3; $total_total_time / $iterations" | bc)
echo "-----------------------------------"
echo "average time to connect: $average_connect_time s"
echo "average total time: $average_total_time s"
}
ping_with_curl_average_for_wg_check
EOL- Make executable:
chmod +x ping_with_curl_average_for_wg_check.sh- In case you don't have
bc, install it:
sudo apt install bc- Run:
./ping_with_curl_average_for_wg_check.sh- Share results and ID key in Nym Operators channel (opens in a new tab)
THANK YOU!
validators
- Validators need to update and prepare for ecash implementation.
Known Bugs & Undone features
- New
nym-nodeswithout a performance 24h history above 50% don't show routing properly onnym-gateway-probe, on Nym Harbourmaster the page may appear blank - we are working on a fix. - Wireguard works on IPv4 only for the time being, we are working on IPv6 implementation.
- Harbourmaster Role column shows
nym-node --mode exit-gatewayasEntryGateway, we are working to fix it. - In rare occassions Harbourmaster shows only "panda" without the "smiley" badge even for nodes, which have T&C's accepted. We are working to fix it.
- Sometimes
nym-noderunning with--wireguard-enabled truegives this error on restart:Serialized netlink packet .. larger than maximum size ..
/home/ubuntu/.cargo/registry/src/index.crates.io-6f17d22bba15001f/defguard_wireguard_rs-0.4.2/src/netlink.rs:155: Serialized netlink packet (23240 bytes) larger than maximum size 12288: NetlinkMessage.From what we found out it seems that one of our dependencies - DefGuard - is failing (opens in a new tab). Based on the reading on their fix, it seems that when node operators try to re-create a wireguard interface with too many previous peers (like on Gateway restart, with restoring from storage), there's an overflow. So their fix is to just add them one by one. To be sure that bumping the dependency version fixes the problem there's still two things we'd need to check - and your feedback would help us a lot:
- Did operators only encounter this error after a
nym-node(Gateway) restart? - Reprouce this error ourselves and see if it actually fixes our problem.
Please share your experience with us to help faster fix of this issue.
v2024.9-topdeck
- Release binaries (opens in a new tab)
- Release CHANGELOG.md (opens in a new tab)
nym-nodeversion1.1.6
- chore: fix 1.80 lint issues (#4731 (opens in a new tab))
- Handle clients with different versions in IPR (#4723 (opens in a new tab))
- Add 1GB/day/user bandwidth cap (#4717 (opens in a new tab))
- Feature/merge back (#4710 (opens in a new tab))
- removed mixnode/gateway config migration code and disabled cli without explicit flag (#4706 (opens in a new tab))
Features
- Removed
nym-mixnodeandnym-gatewayconfig migration code and disabled CLI without explicit flag (opens in a new tab): Gateway and Mixnode commands now won't do anything without explicit--force-runto bypass the deprecation, instead it will tell an operator to run anym-node. The next step, in say a month or so, is to completely remove allclirelated things.
- Verify that the
nym-gatewaybinary andnym-mixnodebinary commands return the_error message_stating to update tonym-node - Check that when adding the
--force-runflag, it still allows the command to be run (aside frominitwhich has been removed) and the message stating to update tonym-nodeis a_warning_now - Check
nym-nodeis not affected - Review the changes in the PR
Scenario 1: Bandwidth Decreasing Continuously'
- Start the client and noted the initial bandwidth (e.g., 1GB).
- Us the client and track bandwidth usage over time (e.g., decrease by 100MB every hour).
- Restart the client after some usage.
- Verify the bandwidth continued from the last recorded value, not reset.
Notes: The bandwidth continued decreasing without resetting upon restart. Logs and reports correctly reflected the decreasing bandwidth.
Scenario 2: Bandwidth Reset Next Day'
- Use the client normally until the end of the day.
- Suspend some clients and kept others active.
- Check bandwidth at midnight.
- Verify that bandwidth reset to 1GB for both suspended and active clients.
Notes: Bandwidth reset to 1GB for all clients at midnight. Logs and reports correctly showed the reset.
Scenario 3: Bandwidth Reset at a Different Time (e.g., Midday)'
- Configure the system to reset bandwidth at midday.
- Use the client and monitored bandwidth until midday.
- Keep the client connected during the reset time.
- Verify that bandwidth reset to 1GB live at midday.
Notes: Bandwidth reset to 1GB at midday while the client was connected. Logs and reports correctly reflected the reset.
- Handle clients with different versions in IPR (opens in a new tab): Allow the IPR to handle clients connecting both using
v6andv7, independently. The motivation is that we want to be able to roll out an API version change gradually for NymVPN clients without breaking backwards compatibility. The main feature on the newv7format that is not yet used, is that it adds signatures for connect/disconnect.
Run the same command (using same gateways deployed from this PR) on different versions of the nym-vpn-cli.
Example:
sudo -E ./nym-vpn-cli -c ../qa.env run --entry-gateway-id $entry_gateway --exit-gateway-id $exit_gateway --enable-two-hop
sudo -E ./nym-vpn-cli -c ../qa.env run --entry-gateway-id $entry_gateway --exit-gateway-id $exit_gateway --enable-two-hopBugfix
-
Feature/merge back (opens in a new tab): Merge back from the release branch the changes that fix the
nym-nodeupgrades. -
Fix version
1.x.xnot having template correspondent initially (opens in a new tab): This should fix the problem of config deserialisation when operators upgrade nodes and skip over multiple versions.
- Tested updating an old nym-node version and ensuring it did not throw any errors.
- Building all binaries is ok
- Running
cargo fmtreturns no issues
Operators Guide updates
- WireGuard tunnel configuration guide for
nym-node(currently Gateways functionalities). For simplicity we made a detailed step by step guide to upgrade an existingnym-nodeto the latest version and configure your VPS routing for WireGuard. Open by clicking on the example block below.
Prerequisites
-
Nym Node Version: You must be running the
2024.9-topdeckrelease branch, which operates asnym-nodeversion1.1.6. You can find the release here: Nym 2024.9-topdeck Release (opens in a new tab). -
Important: Before proceeding, make sure to back up your current
nym-nodeconfiguration to avoid any potential data loss or issues. -
Download Nym Node:
-
You can download the
nym-nodebinary directly using the following command:
curl -L https://github.com/nymtech/nym/releases/download/nym-binaries-v2024.9-topdeck/nym-node -o nym-node && chmod u+x nym-nodeStep 1: Update UFW Firewall Rules
- Warning: Enabling the firewall with UFW without allowing SSH port 22 first will lead to losing access over SSH. Make sure port 22 is allowed before proceeding with any UFW configurations.
Run the following as root or with sudo prefix:
- Check the current status of UFW (Uncomplicated Firewall):
ufw status- Ensure that the following ports are allowed on your machine before adding the WireGuard port:
ufw allow 22/tcp # SSH - you're in control of these ports
ufw allow 80/tcp # HTTP
ufw allow 443/tcp # HTTPS
ufw allow 1789/tcp # Nym specific
ufw allow 1790/tcp # Nym specific
ufw allow 8080/tcp # Nym specific - nym-node-api
ufw allow 9000/tcp # Nym Specific - clients port
ufw allow 9001/tcp # Nym specific - wss port
ufw allow 51822/udp # WireGuard- Confirm that the UFW rules have been updated:
ufw statusStep 2: Download and Prepare the Network Tunnel Manager Script
- Download the
network_tunnel_manager.sh(opens in a new tab) script:
curl -L -o network_tunnel_manager.sh https://github.com/nymtech/nym/blob/develop/scripts/network_tunnel_manager.sh- Make the script executable:
chmod u+x network_tunnel_manager.sh- Apply the WireGuard IPTables rules:
./network_tunnel_manager.sh apply_iptables_rules_wgStep 3: Update the Nym Node Service File
- Modify your
nym-nodeservice file to enable WireGuard. Open the file (usually located at/etc/systemd/system/nym-node.service) and update the[Service]section as follows:
[Service]
User=<YOUR_USER_NAME>
Type=simple
#Environment=RUST_LOG=debug
# CAHNGE PATH IF YOU DON'T RUN IT FROM ROOT HOME DIRECTORY
ExecStart=/root/nym-node run --mode exit-gateway --id <YOUR_NODE_LOCAL_ID> --accept-operator-terms-and-conditions --wireguard-enabled true
Restart=on-failure
RestartSec=30
StartLimitInterval=350
StartLimitBurst=10
LimitNOFILE=65536
[Install]
WantedBy=multi-user.target
# ADD OR TWEAK ANY CUSTOM SETTINGS- Reload the systemd daemon to apply the changes:
systemctl daemon-reload- Restart the
nym-node service:
systemctl restart nym-node.service- Optionally, you can check if the node is running correctly by monitoring the service logs:
journalctl -u nym-node.service -f -n 100Step 4: Run the Network Tunnel Manager Script
Finally, run the following command to initiate our favorite routing test - run the joke through the WireGuard tunnel:
./network_tunnel_manager.sh joke_through_wg_tunnel- Note: Wireguard will return only IPv4 joke, not IPv6. WG IPv6 is under development. Running IPR joke through the mixnet with
./network_tunnel_manager.sh joke_through_the_mixnetshould work with both IPv4 and IPv6!
- Change
--wireguard-enabledflag totrue: With a proper routing configurationnym-nodesrunning as Gateways can now enable WG. See the example below:
For Exit Gateway:
./nym-node run --id <ID> --mode exit-gateway --public-ips "$(curl -4 https://ifconfig.me)" --hostname <HOSTNAME> --http-bind-address 0.0.0.0:8080 --mixnet-bind-address 0.0.0.0:1789 --location <LOCATION> --accept-operator-terms-and-conditions --wireguard-enabled true
# wireguard can be enabled from version 1.1.6 onwardsFor Entry Gateway:
./nym-node run --id <ID> --mode entry-gateway --public-ips "$(curl -4 https://ifconfig.me)" --hostname <HOSTNAME> --http-bind-address 0.0.0.0:8080 --mixnet-bind-address 0.0.0.0:1789 --accept-operator-terms-and-conditions --wireguard-enabled true
# wireguard can be enabled from version 1.1.6 onwards- Update Nym exit policy (opens in a new tab): Based on the survey, AMA and following discussions we added several ports to Nym exit policy. The ports voted upon in the forum governance (opens in a new tab) have not been added yet due to the concerns raised. These ports were unrestricted:
22 # SSH
123 # NTP
445 # SMB file share Windows
465 # URD for SSM
587 # SMTP
853 # DNS over TLS
1433 # databases
1521 # databases
2049 # NFS
3074 # Xbox Live
3306 # databases
5000-5005 # RTP / VoIP
5432 # databases
6543 # databases
8080 # HTTP Proxies
8767 # TeamSpeak
8883 # Secure MQ Telemetry Transport - MQTT over SSL
9053 # Tari
9339 # gaming
9443 # alternative HTTPS
9735 # Lightning
25565 # Minecraft
27000-27050 # Steam and game servers
60000-61000 # MOSH-
Create a NymConnect archive page (opens in a new tab), PR #4750 (opens in a new tab): Archive deprecated NymConnect for backward compatibility, show PEApps examples for both NC and maintained
nym-socks5-client. -
Fix broken URLs and correct redirection. PRs: #4745 (opens in a new tab), #4752 (opens in a new tab) #4755 (opens in a new tab), #4737 (opens in a new tab)
- Use deadlinkchecker.com (opens in a new tab) to go over
nymtech.netand correct all docs URLs - Go over search engines and old medium articles and check that all dead URLs re-directing correctly
- Clarify syntax on
nym-nodesports on VPS setup page (opens in a new tab), PR #4734 (opens in a new tab): Make crystal clear that the addresses and ports in operatorsconfig.tomlmust be opened usingufw(opens in a new tab) and set up as in the example below:
[host]
public_ips = [
'<PUBLIC_IP>'
]
[mixnet]
bind_address = '0.0.0.0:1789'
[http]
bind_address = '0.0.0.0:8080'
[mixnode]
[mixnode.verloc]
bind_address = '0.0.0.0:1790'
[entry_gateway]
bind_address = '0.0.0.0:9000'Tooling
-
Nym Harbourmaster (opens in a new tab) has now several new functionalities:
- Tab for Mixnodes
- Tab with Charts
- New columns with: Moniker (node description), DP delegatee, Accepted T&Cs - also part of a new category 🐼😀
-
Nym has a new Token page (opens in a new tab)
v2024.8-wispa
- Release binaries (opens in a new tab)
- Release CHANGELOG.md (opens in a new tab)
nym-nodeversion1.1.5
- add event parsing to support cosmos_sdk to 0.50 (#4697 (opens in a new tab))
- Fix NR config compatibility (#4690 (opens in a new tab))
- Remove UserAgent constructor since it's weakly typed (#4689 (opens in a new tab))
- [bugfix]: Node_api_check CLI looked over roles on blacklisted nodes (#4687 (opens in a new tab))
- Add mixnodes to self describing api cache (#4684 (opens in a new tab))
- Move and whole bump of crates to workspace and upgrade some (#4680 (opens in a new tab))
- Remove code that refers to removed nym-network-statistics (#4679 (opens in a new tab))
- Remove nym-network-statistics (#4678 (opens in a new tab))
- Create UserAgent that can be passed from the binary to the nym api client (#4677 (opens in a new tab))
- Add authenticator (#4667 (opens in a new tab))
Features
- Default construct NodeRole (opens in a new tab): To preserve compatibility with newer clients interacting with older
nym-api
- Reviewed the changes in the
nym-api-requests/src/models.rsfile. - Verified that the
NymNodeDescriptionstruct includes the newrolefield with a default value set bydefault_node_role. - Checked the implementation of the
default_node_rolefunction to ensure it returnsNodeRole::Inactive. - Ran the updated code in the sandbox environment.
- Monitored the sandbox environment for any issues or errors related to the changes.
Notes (if any):
The test was successful. No issues were flagged during the testing in the sandbox environment. The new default value for NodeRole ensures backward compatibility without causing disruptions.
- [Default construct NodeRole for backwards compatibility (apply #4721 (opens in a new tab) on develop)](https://github.com/nymtech/nym/pull/4722 (opens in a new tab))
- Add upgrades to
nym-nodeforauthenticatorchanges (opens in a new tab)
- Reviewed the changes in the
gateway/src/error.rsandgateway/src/node/mod.rsfiles. - Verified the new error enum
AuthenticatorStartupFailurewas added toGatewayError. - Confirmed the implementation of the
StartedAuthenticatorstruct and its usage in thestart_authenticatorfunction. - Ran the updated code in the canary environment.
- Monitored the canary environment for any issues or errors related to the changes.
- Reviewed the changes in
common/client-libs/validator-client/src/nyxd/cosmwasm_client/client_traits/signing_client.rs,logs.rs,types.rs, andnym-api/src/coconut/tests/mod.rsfiles. - Verified the addition of event parsing in the relevant functions and structs.
- Ensured that the
find_attributefunction correctly parses event attributes. - Ran the updated code in the sandbox environment.
- Broadcasted transactions on the sandbox network to test the changes.
- Monitored the sandbox network for any malformed responses or errors after the test chain upgrade.
- Send bandwidth status messages when connecting (opens in a new tab): When connecting to the gateway we get received the available bandwidth left. Emit a status messages for this, for consumption by the application layer.
- Reviewed the changes in
common/bandwidth-controller/src/event.rs,common/bandwidth-controller/src/lib.rs, andcommon/client-libs/gateway-client/src/client.rsfiles. - Verified the implementation of
BandwidthStatusMessageenum for emitting status messages. - Ensured
GatewayClientis updated to send bandwidth status messages when connecting. - Deployed the updated code on the canary environment.
- Connected to the gateway and checked for the emission of bandwidth status messages.
- Verified that the messages were correctly parsed and consumed by the application layer.
- Ran the VPN client to observe the parsed events.
- Fix NR config compatibility (opens in a new tab): Recently we deleted the old statistics service provider. This fixes some issues where old configs didn't work with the latest changes.
- Make NR able to read config with old keys in
- Remove deleted config keys from NR template
- Reviewed the changes in the
service-providers/network-requester/src/config/mod.rsandservice-providers/network-requester/src/config/template.rsfiles. - Ensured
NetworkRequesterconfig is able to read old keys for compatibility. - Removed old and deleted config keys from the
NetworkRequestertemplate. - Compiled the project to verify no issues or warnings appeared.
- Ran all tests to ensure that the changes did not affect the functionality.
- Validated that no leftover code from the old statistics service provider caused any issues.
- Reviewed the changes in
common/http-api-client/src/user_agent.rsfile. - Verified the removal of the
UserAgentconstructor and ensured that all instances ofUserAgent::neware updated accordingly. - Checked the implementation of
UserAgentstruct usingBinaryBuildInformationandBinaryBuildInformationOwned. - Deployed the updated code across different environments (QA, sandbox, and canary).
- Ran tests to ensure that the
UserAgentstruct functions correctly without the constructor.
- Add mixnodes to self describing api cache (opens in a new tab):
- Abstracts getting the self describing info a bit
- Adds mixnodes to the cache refresher as well
- Adds
rolefield to theNodeDescriptionstruct, to be able to distinguish between mixnodes and gateways - Switched to using
NodeStatusCacheinstead ofContractCache
Called the new /mixnodes/described endpoint as well as the existing /gateways/described endpoint and verified that the data returned for each was correct based on the settings that different nodes have when they are setup.
For gateway endpoint, the “role” for now does not differentiate between entry and exit gateways, this will be implemented in the future.
- Move and whole bump of crates to workspace and upgrade some (opens in a new tab):
- Fix cargo warning for
default_features - Move dirs 4.0 to workspace
- Use workspace
base64dep - Move
rand_chachaandx25519-dalekto workspace - Use workspace
ed25519-dalekdep - Move
itertoolsto workspace deps and upgrade - Move a few partial deps to workspace while preserving versions
- Fix cargo warning for
- Reviewed the changes to move and upgrade crates to the workspace.
- Verified the updated dependencies:
- Moved
dirsto version 4.0 in the workspace. - Updated the
base64dependency to use the workspace version. - Moved
rand_chachaandx25519-dalekto the workspace. - Updated
ed25519-dalekto use the workspace version. - Moved and upgraded
itertoolsin the workspace. - Moved other partial dependencies to the workspace while preserving their versions.
- Moved
- Ensured the
Cargo.tomlfiles across the project reflect these changes correctly. - Compiled the entire project to check for any issues or warnings.
- Verified that all tests pass successfully after the changes.
- Remove
nym-network-statistics(opens in a new tab): Removenym-network-statisticsservice provider that is no longer used.
- Reviewed the project to identify all references to
nym-network-statistics. - Removed all code and dependencies associated with
nym-network-statistics. - Ensured that no references to
nym-network-statisticsremain in the codebase, including comments, imports, and configuration files. - Compiled the project to check for any issues or warnings.
- Ran all tests to ensure the removal did not affect the functionality of the project.
- Remove code that refers to removed
nym-network-statistics(opens in a new tab): Follow up to #4678 (opens in a new tab) where all code interacting with it is removed.
- Reviewed the project to identify all references to
nym-network-statistics. - Removed all code and dependencies associated with
nym-network-statistics. - Ensured that no references to
nym-network-statisticsremain in the codebase, including comments, imports, and configuration files. - Compiled the project to check for any issues or warnings.
- Ran all tests to ensure the removal did not affect the functionality of the project.
- Create
UserAgentthat can be passed from the binary to thenym-apiclient (opens in a new tab):- Support setting
UserAgentfor the validator client - Support setting
UserAgentin the SDKMixnetClient - Set
UserAgentwhen getting the list of gateways and topology innym-clientnym-socks5-client- Standalone
ip-packet-router
- Support setting
Used the nym-vpn-cli to test this, and we can visibly see the UserAgent, no issues with the comments mentioned above.
Example of the user agent sent:
nym-client/1.1.36/x86_64-unknown-linux-gnu/e18bb70
Connected with no problems
Bugfix
Node_api_check.pyCLI looked over roles on blacklisted nodes (opens in a new tab): Removing/correcting this redundant function which results in unwanted error print, will resolve in the program not looking up therolesendpoint for blacklisted GWs, instead just ignores the role description and still return all other endpoints.
Operators Guide updates
- Create a guide to backup and restore
nym-node(opens in a new tab), PR #4720 (opens in a new tab) - Add manual IPv6 ifup/down network configuration (opens in a new tab), PR #4651 (opens in a new tab)
- Extend ISP list (opens in a new tab)
- Add SSL cert bot block to WSS setup (opens in a new tab), PR here (opens in a new tab): WSS setup fully works!
- Correct
HTTP API portin bonding page (opens in a new tab) , PR #4707 (opens in a new tab): ChangeHTTP API portto8080on everynym-nodeby openingconfig.tomland making sure that your binding addresses and ports are as in the block below. Then go to desktop wallet and open the box calledShow advanced optionsand make sure all your ports are set correctly (usually this means to changeHTTP api portto8080formixnodemode).
[host]
public_ips = [
'<PUBLIC_IP>'
]
[mixnet]
bind_address = '0.0.0.0:1789'
[http]
bind_address = '0.0.0.0:8080'
[mixnode]
[mixnode.verloc]
bind_address = '0.0.0.0:1790'
[entry_gateway]
bind_address = '0.0.0.0:9000'- Comment our deprecated node pages in
/docs(opens in a new tab) - Remove redundant syntax from the setup guide (opens in a new tab)
v2024.7-doubledecker
- Release binaries (opens in a new tab)
- Release CHANGELOG.md (opens in a new tab)
nym-nodeversion1.1.4
- Add an early return in
parse_raw_str_logsfor empty raw log strings. (#4686 (opens in a new tab)) - Bump braces from 3.0.2 to 3.0.3 in /wasm/mix-fetch/internal-dev (#4672 (opens in a new tab))
- add expiry returned on import (#4670 (opens in a new tab))
- [bugfix] missing rustls feature (#4666 (opens in a new tab))
- Bump ws from 8.13.0 to 8.17.1 in /wasm/client/internal-dev-node (#4665 (opens in a new tab))
- Bump braces from 3.0.2 to 3.0.3 in /clients/native/examples/js-examples/websocket (#4663 (opens in a new tab))
- Bump ws from 8.14.2 to 8.17.1 in /sdk/typescript/packages/nodejs-client (#4662 (opens in a new tab))
- Update setup.md (#4661 (opens in a new tab))
- New clippy lints (#4660 (opens in a new tab))
- Bump braces from 3.0.2 to 3.0.3 in /nym-api/tests (#4659 (opens in a new tab))
- Bump braces from 3.0.2 to 3.0.3 in /docker/typescript_client/upload_contract (#4658 (opens in a new tab))
- Update vps-setup.md (#4656 (opens in a new tab))
- Update configuration.md (#4655 (opens in a new tab))
- Remove old PR template (#4639 (opens in a new tab))
Features
- Remove the
nym-mixnodeandnym-gatewaybinaries from the CI upload builds action (opens in a new tab) - Add an early return in
parse_raw_str_logsfor empty raw log strings. (opens in a new tab): This accommodates for the v50 + chain upgrade. - Bump braces from
3.0.2to3.0.3in/wasm/mix-fetch/internal-dev(opens in a new tab): Version update of braces (opens in a new tab) - Bump braces from
3.0.2to3.0.3in/clients/native/examples/js-examples/websocket(opens in a new tab): Version update of braces (opens in a new tab). - Bump braces from
3.0.2to3.0.3in/nym-api/tests(opens in a new tab): Version update of braces (opens in a new tab). - Bump braces from
3.0.2to3.0.3in/docker/typescript_client/upload_contract(opens in a new tab): Version update of braces (opens in a new tab). - Bump
wsfrom8.13.0to8.17.1in/wasm/client/internal-dev-node(opens in a new tab): Version update ofws(opens in a new tab). - Bump
wsfrom8.14.2to8.17.1in/sdk/typescript/packages/nodejs-client(opens in a new tab): Version update ofws(opens in a new tab). - Add expiry returned on import (opens in a new tab): We need to return the expiry on import for desktop daemon
nym-vpnd. - New clippy lints (opens in a new tab)
- Remove
nym-connectdirectory (opens in a new tab): Since thenym-vpnhas supersedednym-connect, removenym-connectfrom the repo. - Remove old PR template (opens in a new tab)
Bugfix
- missing rustls feature (opens in a new tab): It just happens to work due to
feature-unification. It should probably have this feature inbuild.
Operators Guide updates
- Node description guide: Steps to add self-description to
nym-nodeand query this information from any node. - Web Secure Socket (WSS) guide and reverse proxy update, PR here (opens in a new tab): A guide to setup
nym-nodein a secure fashion, using WSS via Nginx and Certbot. Landing page (reversed proxy) is updated and simplified.
v2024.6-chomp
- Release binaries (opens in a new tab)
- Release CHANGELOG.md (opens in a new tab)
nym-nodeversion1.1.3- Standalone
nym-gatewayandnym-mixnodebinaries are no longer released
- Remove additional code as part of Ephemera Purge and SP and contracts (#4650 (opens in a new tab))
- bugfix: make sure nym-api can handle non-cw2 (or without detailed build info) compliant contracts (#4648 (opens in a new tab))
- introduced a flag to accept toc and exposed it via self-described API (#4647 (opens in a new tab))
- bugfix: make sure to return an error on invalid public ip (#4646 (opens in a new tab))
- Add ci check for PR having an assigned milestone (#4644 (opens in a new tab))
- Removed ephemera code (#4642 (opens in a new tab))
- Remove stale peers (#4640 (opens in a new tab))
- Add generic wg private network routing (#4636 (opens in a new tab))
- Feature/new node endpoints (#4635 (opens in a new tab))
- standarised ContractBuildInformation and added it to all contracts (#4631 (opens in a new tab))
- validate nym-node public ips on startup (#4630 (opens in a new tab))
- Bump defguard wg (#4625 (opens in a new tab))
- Fix cargo warnings (#4624 (opens in a new tab))
- Update kernel peers on peer modification (#4622 (opens in a new tab))
- Handle v6 and v7 requests in the IPR, but reply with v6 (#4620 (opens in a new tab))
- fix typo (#4619 (opens in a new tab))
- Update crypto and rand crates (#4607 (opens in a new tab))
- Purge name service and service provider directory contracts (#4603 (opens in a new tab))
Features
- Make embedded NR/IPR ignore performance of the Gateway (opens in a new tab): fixes bug in relation to scoring issue on nym-nodes operating as exit gateways failing to come online.
- Introduce a flag to accept Operators Terms and Conditions and exposed it via self-described API (opens in a new tab)
- Verify that the
executefunction correctly checks if theaccept_operator_termsflag is set. - Test that a warning is displayed when the
accept_operator_termsflag is not set. - Confirm that the
NymNodeinstance is initialized withwith_accepted_toc(accepted_toc)when the flag is set. - Apply the
--accept-tocflag in the service and confirmed the change by running:
curl -s -X 'GET' 'http://18.171.251.41:8080/api/v1/auxiliary-details?output=json' -H 'accept: application/json' | jq .accepted_toc- Verify that the output is
true.
- Rename 'accept-toc' flag and fields into explicit 'accept-operator-terms-and-conditions' (opens in a new tab): makes the
accept-tocflag more explicit. - Validate nym-node public ips on startup (opens in a new tab): makes sure
nym-nodeis not run with an emptypublic_ipsand that they do not correspond to common misconfigurations like127.0.0.1or0.0.0.0unless run with--localflag.
- Use the latest release/chomp binary with nym-node and input a dodgy ip
- Validation:
When restarting the node it complains within the service launch file
- New node endpoints (opens in a new tab): introduces new endpoints on nym-api (and creates scaffolding for additional ones) for providing unfiltered network topology alongside performance score of all nodes.
NymApiTopologyProvidergot modified to use those endpoints alongside (configurable) filtering of nodes with score < 50% (like our current blacklist)- Old clients should work as before as no existing endpoint got removed
- Validate that the
skimmedendpoints are working, keeping in mind that they are unstable. The full-fat and semi-skimmed have not yet been implemented.
- Check references to everything named SP and Ephemera and removed any additional references
- Remove additional code as part of Ephemera Purge and SP and contracts (opens in a new tab): in line with #4642 (opens in a new tab) and #4603 (opens in a new tab)
- Check references to everything named SP and Ephemera and removed any additional references
- Add ci check for PR having an assigned milestone (opens in a new tab): add a CI check for checking that a PR is assigned to a milestone. Can bypassed the check by adding a
no-milestonelabel to a PR
- CI complains if no milestone is associated with the an issue.
- Bump defguard wireguard (opens in a new tab)
- Add generic wireguard private network routing (opens in a new tab): as defguard wireguard only allows for peer routing modifications, we will configure the entire wireguard private network to be routed to the wg device. Configuring per peer is also not desirable, as the interface doesn't allow removing routes, so unused ip routing won't be cleaned until gateway restart (and it would also pollute to routing table with a lot of rules when many peers are added).
- This is a part of a bigger ticket, but initial testing has proven to shown that launching nym-nodes (entry and exit gateways) in WG enable mode to be working
QA will use this template for the other related WG tickets in this release milestone.
- Standarise
ContractBuildInformationand add it to all contracts (opens in a new tab): Similarly tocw2, we're now savingContractBuildInformationunder a constant storage key, i.e.b"contract_build_info"that standarises the retrieval by nym-api.- Also each of our contracts now saves and updates that information upon init and migration.
- Use the latest release/chomp contracts and deploy these to QA
- Use the
nym-apito query for the results of these new contracts
curl -X 'GET' \
'https://qa-nym-api.qa.nymte.ch/api/v1/network/nym-contracts-detailed' \
-H 'accept: application/json'- It returns a detailed view of the contracts and which branch they were built from, alongside rust versions and so forth.
- This is a part of a bigger ticket, but initial testing has proven to shown that launching nym-nodes (entry and exit gateways) in WG enable mode to be working. QA will use this template for the other related WG tickets in this release milestone.
- Handle v6 and v7 requests in the IPR, but reply with v6 (opens in a new tab): teach the IPR to read both v6 and v7 requests, but always reply with v6. This is to prepare for bumping to v7 and signed connect/disconnect messages. Follow up PRs will add
- Verify signature
- Send v7 in client with signatures included
- Purge name service and service provider directory contracts (opens in a new tab): this is a compiler assisted purge of the
nym-name-serviceandnym-service-provider-directorycontracts that were never deployed on mainnet, and will anyhow be superseded by the new mixnode directory that is being worked on.
It works insofar that it compiles, we need to deploy and test this on non-mainnet before merging in
- Purge
nym-name-servicecontract - Purge
nym-name-service-common - Purge
nym-service-provider-directorycontract - Purge
nym-service-provider-directory-common - Remove everywhere name-service contract is used
- Remove everywhere sp contract is used
Performed:
- Check references to everything named SP and Ephemera and removed any additional references
Crypto
- Update crypto and rand crates (opens in a new tab): Update sphinx crate to
0.1.1along with 25519 crates andrandcrates
This PR contains a test failure due to the update here (opens in a new tab)
- This is due a change in
x25519-dalekfrom1.1.1to2. - Crypto operations should be identical, but the byte representation has changed (sphinx clamps at creation, x25519 clamps at use). This cannot be changed in the sphinx crate without breaking changes.
- There is a good chance that this failure doesn't impact anything else, but it has to be tested to see.
- A mix of old and new clients with a mix of old and new mixnodes should do
Bugfix
- Make sure nym-api can handle non-cw2 (or without detailed build info) compliant contracts (opens in a new tab): fixes the issue (even if some contracts aren't uploaded on chain it doesn't prohibit the api from working - caveat, the essential vesting and mixnet contract are required)
- Use the latest release/chomp contracts and deploy these to QA
- If the contract was not found, the API would complain of invalid contracts, thus not starting the rest of the operations of the API (network monitor / rewarding etc)
Jun 11 16:27:34 qa-v2-nym-api bash[1352642]: 2024-06-11T16:27:34.551Z ERROR nym_api::nym_contract_cache::cache::refresher - Failed to refresh validator cache - Abci query failed with code 6 - address n14y2x8a60knc5jjfeztt84kw8x8l5pwdgnqg256v0p9v4p7t2q6eswxyusw: no such contract: unknown request
- Make sure to return an error on
nym-nodeinvalid public ip (opens in a new tab): bugfix for #4630 (opens in a new tab) that interestingly hasn't been detected by clippy.
- Use the latest release/chomp binary with nym-node and input a dodgy ip
- Validation:
- Verify that the
establish_connectionfunction correctly attempts to establish a connection to the gateway. - Test error handling for
NetworkConnectionFailedby simulating a failed connection. - Ensure that the
NetworkConnectionFailederror includes theaddressandsourcedetails as expected. - Checked that
SocketState::Availableis set correctly when a connection is successfully established.
- Fix Cargo warnings (opens in a new tab): On every cargo command we have the set warnings:
warning: /home/alice/src/nym/nym/common/dkg/Cargo.toml: default-features is ignored for bls12_381, since default-features was not specified for workspace.dependencies.bls12_381, this could become a hard error in the future warning: /home/alice/src/nym/nym/common/dkg/Cargo.toml: default-features is ignored for ff, since default-features was not specified for workspace.dependencies.ff, this could become a hard error in the future warning: /home/alice/src/nym/nym/common/dkg/Cargo.toml: default-features is ignored for group, since default-features was not specified for workspace.dependencies.group, this could become a hard error in the future warning: /home/alice/src/nym/nym/common/client-libs/validator-client/Cargo.toml: default-features is ignored for bip32, since default-features was not specified for workspace.dependencies.bip32, this could become a hard error in the future warning: /home/alice/src/nym/nym/common/client-libs/validator-client/Cargo.toml: default-features is ignored for prost, since default-features was not specified for workspace.dependencies.prost, this could become a hard error in the future warning: /home/alice/src/nym/nym/common/credentials-interface/Cargo.toml: default-features is ignored for bls12_381, since default-features was not specified for workspace.dependencies.bls12_381, this could become a hard error in the future warning: /home/alice/src/nym/nym/common/credentials/Cargo.toml: default-features is ignored for bls12_381, since default-features was not specified for workspace.dependencies.bls12_381, this could become a hard error in the future warning: /home/alice/src/nym/nym/common/nymcoconut/Cargo.toml: default-features is ignored for bls12_381, since default-features was not specified for workspace.dependencies.bls12_381, this could become a hard error in the future warning: /home/alice/src/nym/nym/common/nymcoconut/Cargo.toml: default-features is ignored for ff, since default-features was not specified for workspace.dependencies.ff, this could become a hard error in the future warning: /home/alice/src/nym/nym/common/nymcoconut/Cargo.toml: default-features is ignored for group, since default-features was not specified for workspace.dependencies.group, this could become a hard error in the future.
- This PR adds
default-features = falseto the workspace dependencies to fix these. An alternative way would be to removedefault-features = falsein the crates, but we assume these were put there for a good reason. Also we might have other crates outside of the main workspace that depends on these crates having default features disabled. - We also have the warning
warning: profile package spec nym-wasm-sdk in profile release did not match any packageswhich we fix by commenting out the profile settings, since the crate is currently commented out in the workspace crate list.
- All binaries have been built and deployed from this branch and no issues have surfaced.
Operators Guide updates
- New Release Cycle introduced: a transparent release flow, including:
- New environments
- Stable testnet
- Testnet token faucet (opens in a new tab)
- Flow chart
- Sandbox testnet guide: teaching Nym node operators how to run their nodes in Nym Sandbox testnet environment.
- Terms & Conditions flag
- Node API Check CLI
- Pruning VPS
syslogscripts - Black-xit: Exiting the blacklist
v2024.5-ragusa
- Release binaries (opens in a new tab)
- Release CHANGELOG.md (opens in a new tab)
nym-nodeversion1.1.2
- Feature/nym node api location (#4605 (opens in a new tab))
- Add optional signature to IPR request/response (#4604 (opens in a new tab))
- Feature/unstable tested nodes endpoint (#4601 (opens in a new tab))
- nym-api: make report/avg_uptime endpoints ignore blacklist (#4599 (opens in a new tab))
- removed blocking for coconut in the final epoch state (#4598 (opens in a new tab))
- allow using explicit admin address for issuing freepasses (#4595 (opens in a new tab))
- Use rfc3339 for last_polled in described nym-api endpoint (#4591 (opens in a new tab))
- Explicitly handle constraint unique violation when importing credential (#4588 (opens in a new tab))
- [bugfix] noop flag for nym-api for nymvisor compatibility (#4586 (opens in a new tab))
- Chore/additional helpers (#4585 (opens in a new tab))
- Feature/wasm coconut (#4584 (opens in a new tab))
- upgraded axum and related deps to the most recent version (#4573 (opens in a new tab))
- Feature/nyxd scraper pruning (#4564 (opens in a new tab))
- Run cargo autoinherit on the main workspace (#4553 (opens in a new tab))
- Add rustls-tls to reqwest in validator-client (#4552 (opens in a new tab))
- Feature/rewarder voucher issuance (#4548 (opens in a new tab))
Features
- New
nym-nodeAPI endpoint/api/v1/auxiliary-details: to expose any additional information. Currently it's just the location.nym-apiwill then query all nodes for that information and put it in theself-describedendpoint. - New
nym-nodelocation available - use one of the three options to add this to your node config:- Update the
locationfield under[host]section ofconfig.toml - For new nodes: Initialise the node with
--locationflag, where they have to provide the country info. Either full country name (e.g. 'Jamaica'), two-letter alpha2 (e.g. 'JM'), three-letter alpha3 (e.g. 'JAM') or three-digit numeric-3 (e.g. '388') can be provided. - For existing nodes: It's also possible to use exactly the same
--locationargument as above, but make sure to also provide--write-changes(or-w) flag to persist those changes!
- Update the
- Feature/unstable tested nodes endpoint (opens in a new tab): Adds new data structures (
TestNode,TestRoute,PartialTestResult) to handle test results for Mixnodes and Gateways. With the inclusion of pagination to handle large API responses efficiently. Lastly, introducing a new route with the tagunstablethus meaning not to be consumed without a user risk, prefixes in endpoints with unstable, are what it says on the tin.
- Deploy new api changes to sandbox environment
- Ensure current operations are transactional and standed operations are working
- Run a script to ensure that the new endpoints are working as expected with pagination
nym-api: make report/avg_uptime endpoints ignore blacklist (opens in a new tab): When querying for node specific data, it's no longer going to go through the entire list of all cached (and filtered nodes) to find it; instead it will attempt to retrieve a single unfiltered entry.
- Build the project and deployed it in a test environment.
- Manually test API endpoints for mixnode and gateway data.
- Verify that the endpoints return the expected data and handle blacklists correctly.
- API performance improved due to the efficient
HashMaplookups - Data in mainnet will differ from test nets due to the increased amount of gateways and mixnodes in that environment
- Test standard uptime routes:
curl -X 'GET' 'https://validator.nymtech.net/api/v1/status/gateway/Fo4f4SQLdoyoGkFae5TpVhRVoXCF8UiypLVGtGjujVPf/avg_uptime' -H 'accept: application/json'- Use rfc3339 for last_polled in described nym-api endpoint (opens in a new tab): Fix issue where the validator-client can't parse the nym-api response for the described endpoint, in particular the
latest_polledfield that was recently added, by making the field userfc3339- Note: This will require upgrading
nym-apiand everything that depends on the described endpoint.
- Note: This will require upgrading
- Update a
nym-apito the binary built from this branch, then restart the api - Check the
journalctlfor error messages - Connected via client and could not see the error messages, this is backwards compatible
- Local testing using sdk examples:
cd <PATH_TO>/nym/sdk/rust/nym-sdk
cargo run --example simple
# outcome
thread 'main' panicked at sdk/rust/nym-sdk/examples/simple.rs:9:64:
called Result::unwrap() on an Err value: ClientCoreError(ValidatorClientError(NymAPIError { source: ReqwestClientError { source: reqwest::Error { kind: Request, url: Url { scheme: "https", cannot_be_a_base: false, username: "", password: None,- Upgrade
axumand related dependencies to the most recent version (opens in a new tab) - Run cargo autoinherit on the main workspace (opens in a new tab): Move several dependencies to the workspace level using cargo autoinherit, to make it easier to keep our dependencies up to date.
- Run cargo autoinherit in the root
- Merge in the new workspace deps in the main list
- We made sure to not mix in other changes as well - all features flags for all crates should be the same as before
- Run
cargo autoinheritin the root directory to move dependencies to the workspace level - Merge the new workspace dependencies into the main list
- Ensure no other changes were mixed in during the process
- Verify that all feature flags for all crates remained the same as before
- Build all the binaries from this branch to confirm successful compilation
- Deploy the built binaries across different environments to ensure there were no issues
- Add rustls-tls to reqwest in validator-client (opens in a new tab): An attempt to make possible to end up in a situation where use use the validator-client but without functioning TLS support. For the monorepo this is masked by cargo feature unification, but becomes a problem for outside consumers, as as been noticed in many of the vpn client implementations.
- In
validator-client:reqwest, enablerustls-tlsfornon-wasm32 - In
client-core: Use default features enabled fornon-wasm32and switch towebpkiroots, since that's what we're using withreqwestanyway - In
gateway-client: Switch towebpkiroots, since that's what we're using withreqwestanyway
- In
Crypto
- Build the project to ensure no compilation errors
- Run tests to verify the functionality of the
issue_credentialfunction - Execute integration tests to check the behaviour during an epoch transition.
- Allow using explicit admin address for issuing freepasses (opens in a new tab)
- Explicitly handle constraint unique violation when importing credential (opens in a new tab): Add a strong type for when a duplicate credential is imported so the vpn lib can handle this.
- Feature/wasm coconut (opens in a new tab): This pull request requires #4585 (opens in a new tab) to be merged first
- Feature/nyxd scraper pruning (opens in a new tab): This PR introduces storage pruning to
nyxdscraper which is then used by the validators rewarder.
- Add a
main.rsfile in thenyxdscraper dir, underneathlib.rs, amendconfig.pruning_options.validate()?;to belet _ = config.pruning_options.validate();in the mod.rs file - Test the different variations of
pruning_options:- Check the default option:
pruning_options: PruningOptions::default() - Check the nothing option:
pruning_options: PruningOptions::nothing() - Check the custom option, example:
pruning_options: PruningOptions { keep_recent: (500), interval: (10), strategy: (PruningStrategy::Custom) } - Check the pruning in real life for the validator rewarder
- Check the default option:
- Validate that the database table
blockswas being updated accordingly
- Feature/rewarder voucher issuance (opens in a new tab)
- Introduces signature checks on issued credential data
- Stores evidence of any failures/malicious behaviour in the internal db
Bugfix
noopflag fornym-apifornymvisorcompatibility (opens in a new tab)- The application starts correctly and logs the starting message
- The
--no_bannerflag works as intended, providing compatibility withnymvisor
- Build the project to ensure no compilation errors
- Run the binary with different command-line arguments to verify the CLI functionality
- Test with and without the
--no_bannerflag to ensure compatibility and expected behavior - Verify logging setup and configuration file parsing
Operators Guide updates
nym-gateway-probe: A CLI tool to check in-real-time networking status of any Gateway locally.- Where to host your
nym-node?: A list of Internet Service Providers (ISPs) by Nym Operators community. We invite all operators to add their experiences with different ISPs to strengthen the community knowledge and Nym mixnet performance. - Make sure you run
nym-nodewith--wireguard-enabled falseand add a location description to yourconfig.toml, both documented innym-nodesetup manual.
v2024.4-nutella
- Merged PRs (opens in a new tab)
nym-nodeversion1.1.1- This release also contains:
nym-gatewayandnym-network-requesterbinaries - core improvements on nym-node configuration
- Nym wallet changes:
- Adding
nym-nodecommand to bonding screens - Fixed the delegation issues with fixing RPC
- Adding
- Network configuration section updates, in particular for
--mode mixnodeoperators - VPS IPv6 troubleshooting updates
v2024.3-eclipse
- Release Changelog.md (opens in a new tab)
nym-nodeinitial release- New tool for monitoring Gateways performance harbourmaster.nymtech.net (opens in a new tab)
- New versioning
1.1.0+nymnodemainly for internal migration testing, not essential for operational use. We aim to correct this in a future release to ensure mixnodes feature correctly in the main API - New VPS specs & configuration page
- New configuration page with connectivity setup guide - a new requirement for
exit-gateway - API endpoints redirection: Nym-mixnode and nym-gateway endpoints will eventually be deprecated; due to this, their endpoints will be redirected to new routes once the
nym-nodehas been migrated and is running
API endpoints redirection
| Previous endpoint | New endpoint |
|---|---|
http://<IP>:8000/stats | http://<IP>:8000/api/v1/metrics/mixing |
http://<IP>:8000/hardware | http://<IP>:8000/api/v1/system-info |
http://<IP>:8000/description | http://<IP>:8000/api/v1/description |